
Edge Security Market
Edge Security Market Forecasts to 2030 - Global Analysis By Component (CASB, Implementation & Integration, SASE, SD-WAN, Services, Solutions, Support & Maintenance and Training & Consulting), Deployment Mode, Organization Size, End User and By Geography

According to Stratistics MRC, the Global Edge Security Market is accounted for $23.73 billion in 2023 and is expected to reach $104.58 billion by 2030 growing at a CAGR of 23.6% during the forecast period. The Edge Security is a subsegment of the cybersecurity market that focuses on protecting and securing networks, devices, and data at the edge of network architecture. Computer resources and data that are located closer to end users or devices are referred to as being on the edge, as opposed to being centralized in a data center or the cloud. Devices at the network's edge, such as edge servers, gateways, smartphones, and other IoT (Internet of Things) devices, are handled by edge security solutions.
According to the AT&T Cybersecurity Insights Report 2022, 5G and cloud are the most preferred edge networks. The report found that over 93% of respondents researched, implemented, and completed 5G implementations, and 58% believed the cellular edge would enable near-real-time cloud services.
Market Dynamics:
Driver:
Need for secure access to cloud services and websites
One of the main use cases for the security service edge is enforcing policy control over user access to the internet, online, and cloud services (historically carried out by a SWG). Risk is reduced while end users access content both on and off the network because of SSE policy management. Secure access to IaaS, PaaS, and SaaS is also significantly influenced by compliance with corporate internet and access control policies. Cloud Security Posture Management (CSPM), which guards against unsafe misconfigurations that might result in breaches, is another crucial function.
Restraint:
Managing highly distributed environments
Managing any large-scale edge architecture entails managing a huge number of smaller IT environments—possibly thousands. It is time-consuming to manually update activities like configuration management, OS patches, and other software updates. Large-scale distributed infrastructure deployment and management are difficult enough without adding unpredictability and silos to the equation. Therefore, administration and automation are crucial for tasks like centralized application updates, event-driven action, and bulk configuration. For managing edge computing environments, standardized operating system settings and cluster orchestration are crucial.
Opportunity:
Increasing adoption of 5G services
Edge computing and 5G are related technologies. Both of these have the potential to greatly enhance application performance and allow for the real-time processing of enormous volumes of data. While mobile edge computing lowers latency by introducing processing capabilities into the network closer to the end user, 5G speeds up communication by up to ten times that of 4G. Ultra-Reliable Low Latency Communication (URLLC), which enables applications like V2X and Telesurgery, Cobots, and more, will be supported by 5G due to a jump in technology. End-to-end latency for these applications must be measured in milliseconds. Enhanced Mobile Broadband (eMBB) will be a feature of 5G that will be available for use cases requiring high data rates, like virtual and augmented reality.
Threat:
Lack of awareness and education about SASE security architecture
Numerous businesses had to speed up their digital transformation efforts in response to the COVID-19 epidemic in order to accommodate work from anywhere and remote operations. Security and IT professionals said that 84% of firms recently increased their digital transformation adoption projects and shifted to the cloud in the Versa Networks Global Transformation Survey 2021. The two biggest problems encountered during this shift were network performance and security. As a result of the numerous new devices being connected to enterprises' networks, the systems became overwhelmed, and security concerns sharply increased.
Covid-19 Impact:
Enterprises increasingly favor e-learning and remote working platforms as a result of the COVID 19 pandemic. Business networks have experienced an increase in demands for access due to the growing acceptance of remote working. Due to this circumstance, the firm's networks experienced higher traffic volumes and more data encryption traffic. The need for a sophisticated network solution is therefore anticipated to increase. Furthermore, even after the pandemic, it is projected that these security solutions will become more popular in specific industries.
The managed services segment is expected to be the largest during the forecast period
Throughout the projected period, Managed Service Providers (MSPs) held the majority of the market share, which includes administering databases and data collection. Managed Security Service Providers (MSSPs) give other businesses specialized security services. Managed Security Services (MSSs) come in a variety of forms, including cloud services, sophisticated fraud investigators, on-premises device monitoring and management services, and pure system administration. The managed services industry is highly fragmented and made up of vendors from a variety of industries, including specialized MSS providers, security experts, system integrators, and VARs.
The cloud segment is expected to have the highest CAGR during the forecast period
As a result of distributed edge expansion that expands the attack surface and strengthens the demand for security at each site, the cloud segment is predicted to experience profitable growth during the forecasted period. For multi-cloud, hybrid-cloud, and multi-tenant edge deployments, cloud-based edge security solutions provide a solution. Through the implementation of a zero-trust security model across all edge locations, it provides tested solutions for IoT, API, LAN, and application security. The difficulties in administering older application-based solutions are removed by edge security solutions built on the cloud.
Region with largest share:
Due to the business dynamism, pillars, essential institutional pillars, strong innovation environment, and financing mechanism, the North American region experienced the most economic share in the edge security market throughout the anticipated period. With the increased use of edge computing and the greater acceptance of IoT and 5G services in the area, there is a growing need for edge security solutions. Additionally, the region serves as a hub for a large number of edge security solution providers who are funding R&D to create cutting-edge products and services.
Region with highest CAGR:
The Asia-Pacific region is anticipated to grow rapidly during the extended timeframe. The area is home to several advanced economies, including China, Japan, Australia, and New Zealand. Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) are areas where the region thrives. This will probably fuel the expansion of the local edge security sector. In contrast to North America and Europe, the Asia-Pacific region has a lower adoption rate. According to the Sophos Future of Cybersecurity Asia Pacific and Japan 2022 report, this is primarily due to a shortage of knowledgeable cybersecurity specialists and a lack of awareness among leading IT professionals.
Key players in the market
Some of the key players in Edge Security market include Akamai Technologies Inc, Amazon Web Services, Inc, Broadcom, Inc, Check Point Software Technologies Ltd, Cisco Systems, Inc, Cloud Software Group, Inc, Cloudflare, Inc, F5 Networks, Inc, Forcepoint LLC (Francisco Partners), Fortinet, Inc, IBM Corporation, Jupiter Networks, Inc, Microsoft Corporation , Palo Alto Networks, Inc and Zscaler Softech India Private Limited.
Key Developments:
In October 2022, Fortinet announced significant cloud-delivered enhancements to FortiSASE to enable secure internet access that ensures consistent security for all user traffic to and from the internet. FortiSASE now includes new updates enhancing support for secure private and SaaS access cases.
In October 2022, Zscaler came into partnership with DYXnet, a member of NEOLINK and a carrier-neutral enterprise network service provider across China. Under this partnership, companies would launch the DYXnet SASE solution. With the solution customers could streamline security operations in the cloud, building a seamless user experience while protecting their IT infrastructures against the onslaught of cyber threats.
In September 2022: Palo Alto Networks partnered with Wipro, an India-based Information technology company. With this partnership, the company would deliver its customers' complete platforms with managed services to support customers protect the cloud, and network and broadening their edge in a way that is combined, simple, and automated.
In Aug-2022, Fortinet came into partnership with Comcast Business, a provider of big business capabilities and development to small businesses at affordable prices. Through this partnership, Fortinet would create SASE services that help customers at any stage of digital advancement with Fortinet's industry-leading security-driven networking technology.
In June 2022, Cisco joined hands with Kyndryl, a provider of IT infrastructure services. Under this partnership, companies would help enterprise customers boost their transformation into data-driven businesses powered by Cisco solutions and Kyndryl managed services.
In March 2022, Fortinet partnered with Orange Business Services, a global integrator of communications products and services. In this partnership, both companies would aim to provide a disruptive approach to Secure Access Service Edge (SASE). The approach consists of integration and automation allowing real-time service updates and an unparalleled user experience.
In February 2022, Check Point acquired Spectral, an innovator in automated code security. With this acquisition, Check Point would enhance its Cloud Guard solution with a developer-first security platform and provide the widest range of cloud application security.
Components Covered:
• CASB
• Implementation & Integration
• SASE
• SD-WAN
• Services
• Solutions
• Support & Maintenance
• Training & Consulting
Deployment Modes Covered:
• Cloud
• On Premises
Organization Sizes Covered:
• Small & Medium Sized Enterprises (SMEs)
• Large Enterprises
End Users Covered:
• Banking, Financial Services & Insurance (BFSI)
• Energy & Utilities
• Government & Defense
• Healthcare
• IT & Telecom
• Manufacturing
• Retail
• Other End Users
Regions Covered:
• North America
o US
o Canada
o Mexico
• Europe
o Germany
o UK
o Italy
o France
o Spain
o Rest of Europe
• Asia Pacific
o Japan
o China
o India
o Australia
o New Zealand
o South Korea
o Rest of Asia Pacific
• South America
o Argentina
o Brazil
o Chile
o Rest of South America
• Middle East & Africa
o Saudi Arabia
o UAE
o Qatar
o South Africa
o Rest of Middle East & Africa
What our report offers:
- Market share assessments for the regional and country-level segments
- Strategic recommendations for the new entrants
- Covers Market data for the years 2021, 2022, 2023, 2026, and 2030
- Market Trends (Drivers, Constraints, Opportunities, Threats, Challenges, Investment Opportunities, and recommendations)
- Strategic recommendations in key business segments based on the market estimations
- Competitive landscaping mapping the key common trends
- Company profiling with detailed strategies, financials, and recent developments
- Supply chain trends mapping the latest technological advancements
Free Customization Offerings:
All the customers of this report will be entitled to receive one of the following free customization options:
• Company Profiling
o Comprehensive profiling of additional market players (up to 3)
o SWOT Analysis of key players (up to 3)
• Regional Segmentation
o Market estimations, Forecasts and CAGR of any prominent country as per the client's interest (Note: Depends on feasibility check)
• Competitive Benchmarking
Benchmarking of key players based on product portfolio, geographical presence, and strategic alliances
Table of Contents
1 Executive Summary
2 Preface
2.1 Abstract
2.2 Stake Holders
2.3 Research Scope
2.4 Research Methodology
2.4.1 Data Mining
2.4.2 Data Analysis
2.4.3 Data Validation
2.4.4 Research Approach
2.5 Research Sources
2.5.1 Primary Research Sources
2.5.2 Secondary Research Sources
2.5.3 Assumptions
3 Market Trend Analysis
3.1 Introduction
3.2 Drivers
3.3 Restraints
3.4 Opportunities
3.5 Threats
3.6 End User Analysis
3.7 Emerging Markets
3.8 Impact of Covid-19
4 Porters Five Force Analysis
4.1 Bargaining power of suppliers
4.2 Bargaining power of buyers
4.3 Threat of substitutes
4.4 Threat of new entrants
4.5 Competitive rivalry
5 Global Edge Security Market, By Component
5.1 Introduction
5.2 CASB
5.3 Implementation & Integration
5.4 SASE
5.5 SD-WAN
5.6 Services
5.6.1 Managed Services
5.6.2 Professional Services
5.6.2.1 Support & Maintenance Services
5.6.2.2 Training & Consulting Services
5.6.2.3 Implementation & Integration Services
5.7 Solutions
5.7.1 Secure Access Service Edge
5.7.2 Software Defined Wide Area Network
5.7.3 Cloud Access Security Broker
5.7.4 Other Solutions
5.8 Support & Maintenance
5.9 Training & Consulting
6 Global Edge Security Market, By Deployment Mode
6.1 Introduction
6.2 Cloud
6.3 On Premises
7 Global Edge Security Market, By Organization Size
7.1 Introduction
7.2 Small & Medium Sized Enterprises (SMEs)
7.3 Large Enterprises
8 Global Edge Security Market, By End User
8.1 Introduction
8.2 Banking, Financial Services & Insurance (BFSI)
8.3 Energy & Utilities
8.4 Government & Defense
8.5 Healthcare
8.6 IT & Telecom
8.7 Manufacturing
8.8 Retail
8.9 Other End Users
9 Global Edge Security Market, By Geography
9.1 Introduction
9.2 North America
9.2.1 US
9.2.2 Canada
9.2.3 Mexico
9.3 Europe
9.3.1 Germany
9.3.2 UK
9.3.3 Italy
9.3.4 France
9.3.5 Spain
9.3.6 Rest of Europe
9.4 Asia Pacific
9.4.1 Japan
9.4.2 China
9.4.3 India
9.4.4 Australia
9.4.5 New Zealand
9.4.6 South Korea
9.4.7 Rest of Asia Pacific
9.5 South America
9.5.1 Argentina
9.5.2 Brazil
9.5.3 Chile
9.5.4 Rest of South America
9.6 Middle East & Africa
9.6.1 Saudi Arabia
9.6.2 UAE
9.6.3 Qatar
9.6.4 South Africa
9.6.5 Rest of Middle East & Africa
10 Key Developments
10.1 Agreements, Partnerships, Collaborations and Joint Ventures
10.2 Acquisitions & Mergers
10.3 New Product Launch
10.4 Expansions
10.5 Other Key Strategies
11 Company Profiling
11.1 Akamai Technologies Inc
11.2 Amazon Web Services, Inc
11.3 Broadcom, Inc
11.4 Check Point Software Technologies Ltd
11.5 Cisco Systems, Inc
11.6 Cloud Software Group, Inc
11.7 Cloudflare, Inc
11.8 F5 Networks, Inc
11.9 Forcepoint LLC (Francisco Partners)
11.10 Fortinet, Inc
11.11 IBM Corporation
11.12 Jupiter Networks, Inc
11.13 Microsoft Corporation
11.14 Palo Alto Networks, Inc
11.15 Zscaler Softech India Private Limited
List of Tables
1 Global Edge Security Market Outlook, By Region (2021-2030) ($MN)
2 Global Edge Security Market Outlook, By Component (2021-2030) ($MN)
3 Global Edge Security Market Outlook, By CASB (2021-2030) ($MN)
4 Global Edge Security Market Outlook, By Implementation & Integration (2021-2030) ($MN)
5 Global Edge Security Market Outlook, By Managed Services (2021-2030) ($MN)
6 Global Edge Security Market Outlook, By Other Solutions (2021-2030) ($MN)
7 Global Edge Security Market Outlook, By Professional Services (2021-2030) ($MN)
8 Global Edge Security Market Outlook, By SASE (2021-2030) ($MN)
9 Global Edge Security Market Outlook, By SD-WAN (2021-2030) ($MN)
10 Global Edge Security Market Outlook, By Services (2021-2030) ($MN)
11 Global Edge Security Market Outlook, By Managed Services (2021-2030) ($MN)
12 Global Edge Security Market Outlook, By Professional Services (2021-2030) ($MN)
13 Global Edge Security Market Outlook, By Solutions (2021-2030) ($MN)
14 Global Edge Security Market Outlook, By Secure Access Service Edge (2021-2030) ($MN)
15 Global Edge Security Market Outlook, By Software Defined Wide Area Network (2021-2030) ($MN)
16 Global Edge Security Market Outlook, By Cloud Access Security Broker (2021-2030) ($MN)
17 Global Edge Security Market Outlook, By Other Solutions (2021-2030) ($MN)
18 Global Edge Security Market Outlook, By Support & Maintenance (2021-2030) ($MN)
19 Global Edge Security Market Outlook, By Training & Consulting (2021-2030) ($MN)
20 Global Edge Security Market Outlook, By Deployment Mode (2021-2030) ($MN)
21 Global Edge Security Market Outlook, By Cloud (2021-2030) ($MN)
22 Global Edge Security Market Outlook, By On Premises (2021-2030) ($MN)
23 Global Edge Security Market Outlook, By Organization Size (2021-2030) ($MN)
24 Global Edge Security Market Outlook, By Small & Medium Sized Enterprises (SMEs) (2021-2030) ($MN)
25 Global Edge Security Market Outlook, By Large Enterprises (2021-2030) ($MN)
26 Global Edge Security Market Outlook, By End User (2021-2030) ($MN)
27 Global Edge Security Market Outlook, By Banking, Financial Services & Insurance (BFSI) (2021-2030) ($MN)
28 Global Edge Security Market Outlook, By Energy & Utilities (2021-2030) ($MN)
29 Global Edge Security Market Outlook, By Government & Defense (2021-2030) ($MN)
30 Global Edge Security Market Outlook, By Healthcare (2021-2030) ($MN)
31 Global Edge Security Market Outlook, By IT & Telecom (2021-2030) ($MN)
32 Global Edge Security Market Outlook, By Manufacturing (2021-2030) ($MN)
33 Global Edge Security Market Outlook, By Retail (2021-2030) ($MN)
34 Global Edge Security Market Outlook, By Other End Users (2021-2030) ($MN)
Note: Tables for North America, Europe, APAC, South America, and Middle East & Africa Regions are also represented in the same manner as above.
List of Figures
RESEARCH METHODOLOGY
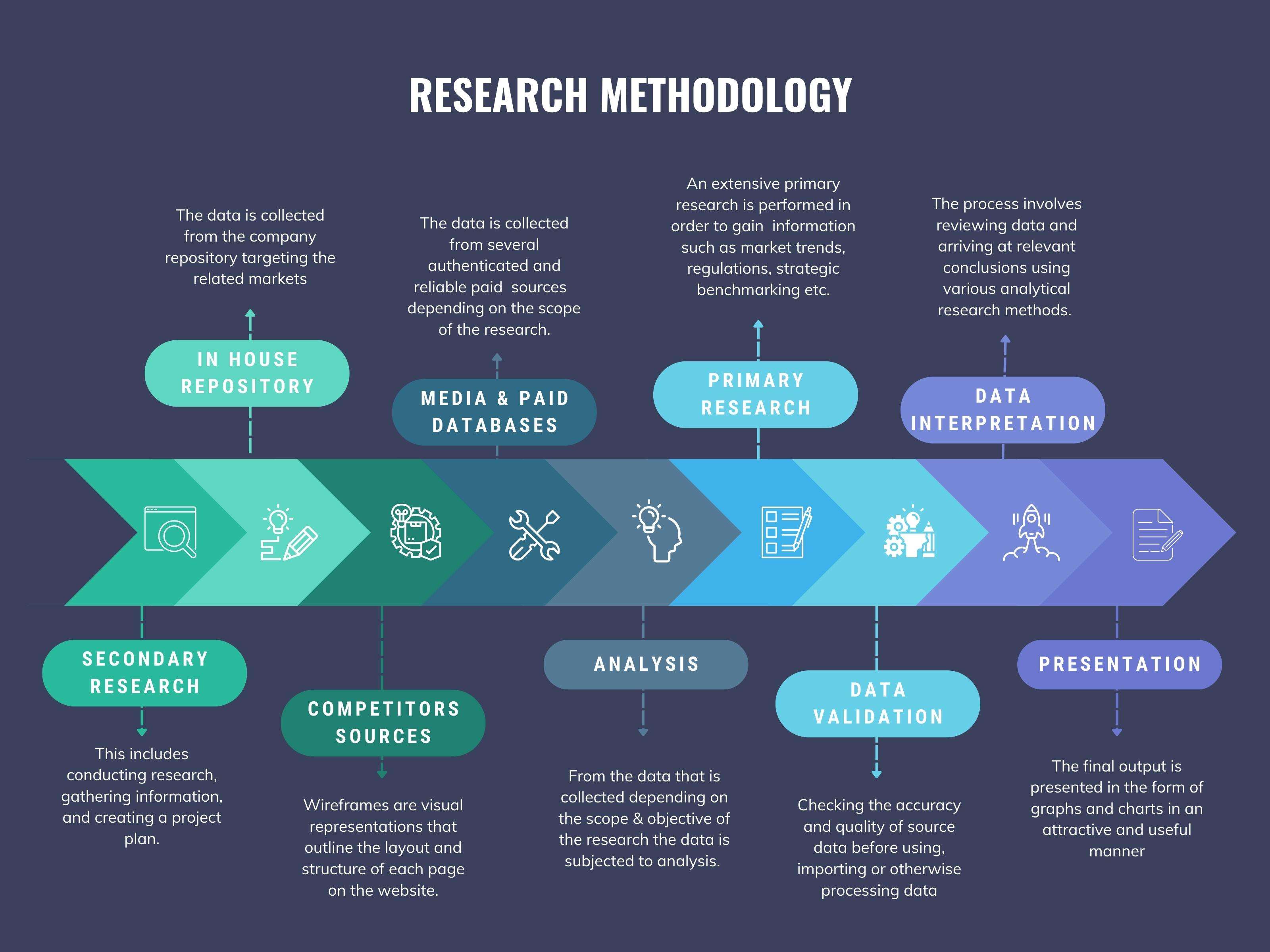
We at ‘Stratistics’ opt for an extensive research approach which involves data mining, data validation, and data analysis. The various research sources include in-house repository, secondary research, competitor’s sources, social media research, client internal data, and primary research.
Our team of analysts prefers the most reliable and authenticated data sources in order to perform the comprehensive literature search. With access to most of the authenticated data bases our team highly considers the best mix of information through various sources to obtain extensive and accurate analysis.
Each report takes an average time of a month and a team of 4 industry analysts. The time may vary depending on the scope and data availability of the desired market report. The various parameters used in the market assessment are standardized in order to enhance the data accuracy.
Data Mining
The data is collected from several authenticated, reliable, paid and unpaid sources and is filtered depending on the scope & objective of the research. Our reports repository acts as an added advantage in this procedure. Data gathering from the raw material suppliers, distributors and the manufacturers is performed on a regular basis, this helps in the comprehensive understanding of the products value chain. Apart from the above mentioned sources the data is also collected from the industry consultants to ensure the objective of the study is in the right direction.
Market trends such as technological advancements, regulatory affairs, market dynamics (Drivers, Restraints, Opportunities and Challenges) are obtained from scientific journals, market related national & international associations and organizations.
Data Analysis
From the data that is collected depending on the scope & objective of the research the data is subjected for the analysis. The critical steps that we follow for the data analysis include:
- Product Lifecycle Analysis
- Competitor analysis
- Risk analysis
- Porters Analysis
- PESTEL Analysis
- SWOT Analysis
The data engineering is performed by the core industry experts considering both the Marketing Mix Modeling and the Demand Forecasting. The marketing mix modeling makes use of multiple-regression techniques to predict the optimal mix of marketing variables. Regression factor is based on a number of variables and how they relate to an outcome such as sales or profits.
Data Validation
The data validation is performed by the exhaustive primary research from the expert interviews. This includes telephonic interviews, focus groups, face to face interviews, and questionnaires to validate our research from all aspects. The industry experts we approach come from the leading firms, involved in the supply chain ranging from the suppliers, distributors to the manufacturers and consumers so as to ensure an unbiased analysis.
We are in touch with more than 15,000 industry experts with the right mix of consultants, CEO's, presidents, vice presidents, managers, experts from both supply side and demand side, executives and so on.
The data validation involves the primary research from the industry experts belonging to:
- Leading Companies
- Suppliers & Distributors
- Manufacturers
- Consumers
- Industry/Strategic Consultants
Apart from the data validation the primary research also helps in performing the fill gap research, i.e. providing solutions for the unmet needs of the research which helps in enhancing the reports quality.
For more details about research methodology, kindly write to us at info@strategymrc.com
Frequently Asked Questions
In case of any queries regarding this report, you can contact the customer service by filing the “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
Yes, the samples are available for all the published reports. You can request them by filling the “Request Sample” option available in this page.
Yes, you can request a sample with your specific requirements. All the customized samples will be provided as per the requirement with the real data masked.
All our reports are available in Digital PDF format. In case if you require them in any other formats, such as PPT, Excel etc you can submit a request through “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
We offer a free 15% customization with every purchase. This requirement can be fulfilled for both pre and post sale. You may send your customization requirements through email at info@strategymrc.com or call us on +1-301-202-5929.
We have 3 different licensing options available in electronic format.
- Single User Licence: Allows one person, typically the buyer, to have access to the ordered product. The ordered product cannot be distributed to anyone else.
- 2-5 User Licence: Allows the ordered product to be shared among a maximum of 5 people within your organisation.
- Corporate License: Allows the product to be shared among all employees of your organisation regardless of their geographical location.
All our reports are typically be emailed to you as an attachment.
To order any available report you need to register on our website. The payment can be made either through CCAvenue or PayPal payments gateways which accept all international cards.
We extend our support to 6 months post sale. A post sale customization is also provided to cover your unmet needs in the report.
Request Customization
We offer complimentary customization of up to 15% with every purchase. To share your customization requirements, feel free to email us at info@strategymrc.com or call us on +1-301-202-5929. .
Please Note: Customization within the 15% threshold is entirely free of charge. If your request exceeds this limit, we will conduct a feasibility assessment. Following that, a detailed quote and timeline will be provided.
WHY CHOOSE US ?

Assured Quality
Best in class reports with high standard of research integrity

24X7 Research Support
Continuous support to ensure the best customer experience.

Free Customization
Adding more values to your product of interest.

Safe & Secure Access
Providing a secured environment for all online transactions.

Trusted by 600+ Brands
Serving the most reputed brands across the world.
