
Industrial Cyber Security Market
Industrial Cyber Security Market Forecasts to 2030 - Global Analysis By Security Type (Network Security, Application Security, Wireless Security, Cloud Security, Endpoint Security and Other Types), Deployment Component (Services, Solutions and Other Components), Offering, Deployment Mode, End-User and By Geography

|
Years Covered |
2021-2030 |
|
Estimated Year Value (2023) |
US $19.0 BN |
|
Projected Year Value (2030) |
US $25.6 BN |
|
CAGR (2023 - 2030) |
4.4% |
|
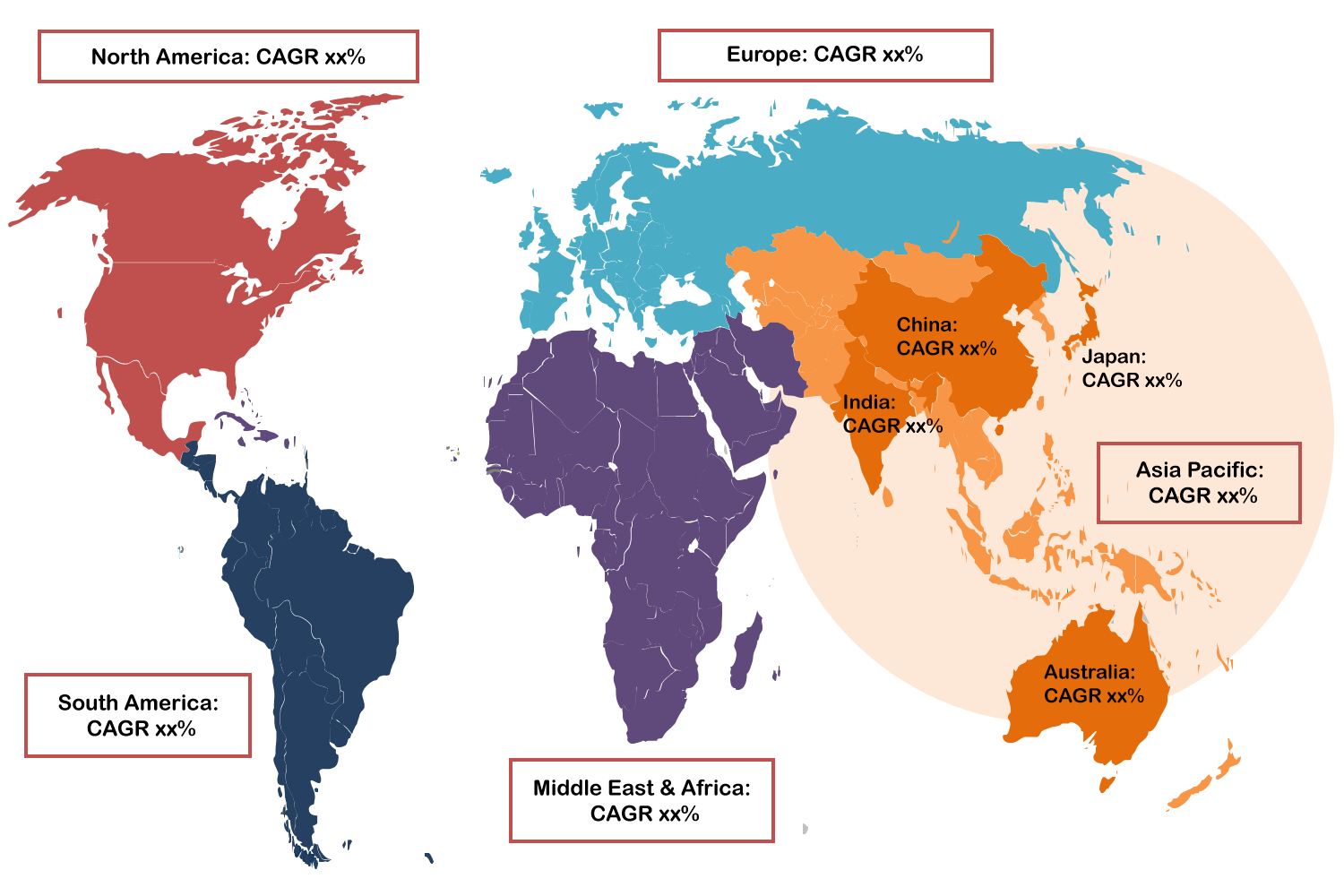
Regions Covered |
North America, Europe, Asia Pacific, South America, and Middle East & Africa |
|
Countries Covered |
US, Canada, Mexico, Germany, UK, Italy, France, Spain, Japan, China, India, Australia, New Zealand, South Korea, Rest of Asia Pacific, South America, Argentina, Brazil, Chile, Middle East & Africa, Saudi Arabia, UAE, Qatar, and South Africa |
|
Largest Market |
North America |
|
Highest Growing Market |
Asia Pacific |
According to Stratistics MRC, the Global Industrial Cyber Security Market is accounted for $19.0 billion in 2023 and is expected to reach $25.6 billion by 2030 growing at a CAGR of 4.4% during the forecast period. The process of defending industrial control systems from risks from cyber attackers is known as industrial cyber security. It is frequently referred to as security or OT security. Industries like energy, power utilities, transportation, manufacturing, and chemicals are among those that utilize industrial cyber security the most frequently. They assist in the distribution process as well as remotely automating and controlling the manufacturing of goods.
According to Trend Micro Incorporated (Japan), in 2020, 61% of manufacturers experienced cybersecurity incidents in their smart factories. These attacks disrupted manufacturing processes, leading to production delays and irreversible loss of capital and critical & confidential data.
Market Dynamics:
Driver:
Emergence of Disruptive Digital Technologies
The rise in cyber attacks driven by technological improvements, cyber security has become the primary concern for businesses in the industrial sector. Due to the increased adoption of cutting-edge technologies like machine learning, data analytics, robots, and the IIoT, the industrial sector is becoming more and more exposed to cyber threats. Initiatives are being taken by government agencies and several organisations to encourage the use of cutting-edge technologies in the industrial sector. Furthermore, it also expands the window for online criminals to exploit vulnerable systems and networks.
Restraint:
Lack of knowledge and experts
Although industrial cybersecurity solutions have many benefits, the majority of end-users in developing nations in the Asia Pacific, Middle East, Africa, and South America are unaware of these services. The development of the worldwide industrial cyber security market is also anticipated to be hampered by a shortage of qualified individuals to create and manage industrial cyber security solutions in developing nations, where cyber attacks are on the rise. Security hackers have developed new hazards as technology has developed. Traditional cyber security systems find it difficult to detect and counteract these emerging attacks.
Opportunity:
IoT integration into industrial control systems is receiving more attention.
The IoT has greatly facilitated the completion of challenging activities and made millions of people's lives better. It enables contemporary companies a new method for controlling, storing, and processing data in data centres and the cloud. Industrial organisations are able to make better use of a significant amount of data produced in their facilities by implementing IoT technologies. The way that consumers, businesses, and communication service providers engage with one another has been completely transformed by smart gadgets. They have made it possible for various business processes to be automated and adaptable. There are now more people using smartphones globally, which has raised the number of interconnected devices using multiple platforms. These devices are connected to each other through wireless cellular and non-cellular networks such as Zigbee, Bluetooth, 3G, 4G, and upcoming 5G.
Threat:
Misunderstanding the hazards and underestimating their severity
The operational setting is now able to be understood and analysed by the industry workers due to the continual evolution of the industrial control system, which has begun to include a wide range of networked devices. It exposes the system to the risk of hackers though. Owners of industrial firms and their staff tend to underestimate the current and impending likely risks in the ICS environment because targeted assaults against automation systems are relatively uncommon, and due to is an excessive dependence on safety precautions.Typically, operational technologies (OTs) are not fully described in historical threats, which is typically security products and related technologies are built. Therefore, synthetic attacks are protected against in industrial control systems. As a result, security tools and software are created without addressing potential dangers or threats or the nature of future attacks and without a thorough analysis and scrutiny of a day-to-day threat landscape. As a result, real-world threats are underestimated.
Covid-19 Impact:
During the COVID-19 epidemic, governments around the world laid restrictions that encouraged employees to work from home. A segment of the IT security industry has been badly affected by the combat measures, such as complete lockdowns and quarantine. due to its impact on manufacturing activities, the COVID-19 pandemic had an effect on the industrial sector. Manufacturing is becoming smarter through technology and connected devices as advanced technologies like AI, machine learning, and IoT are being adopted more frequently. The COVID-19 incident was used by a number of top cybersecurity players as a chance to examine and restructure their current tactics and build out cutting-edge portfolios. Due to the rise in cyber attacks during the pandemic, businesses are better equipped to develop responses more quickly. Thus, the rising demand for cybersecurity solutions in the industrial sector is expected to create significant opportunities for the growth of the industrial cybersecurity market in the coming years.
The solutions segment is expected to be the largest during the forecast period
The solutions segment is expected to be the largest during the forecast period. The solutions initiative is most likely to get a significant share of the market in industrial cybersecurity. The main driver of this expansion is the growing demand for software products like DDoS, firewalls, SCADA encryption, virtualization security antivirus/malware, backup & recovery, and many others. Leaders in the industry are focusing on developing and delivering cutting-edge industrial security software solutions for the automotive, oil & gas, energy, and other sectors. Check Point Software Technologies Ltd. released Check Point R81 in November, a unified cybersecurity platform designed for industrial applications. The platform assists in delivering pre-programmed alerts for threat protection, assisting the IT personnel in efficiently managing complex network settings.
The network security segment is expected to have the highest CAGR during the forecast period
The network security segment is expected to have the highest CAGR during the forecast period. Network security refers to security services and tools used to spot and avoid online threats in computer networks and networked resources. Examples of network security solutions include firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), encryption software, identity and access management (IAM), united threat management (UTM), online and email security solutions, antivirus software, and antispyware software. These solutions help safeguard data against threats including SQL injection, cross-site scripting, and DDoS attacks.
Region with largest share:
North America is expected to have the largest share during the forecast period. The investigation of the North American industrial cybersecurity market includes both the United States and Canada. The challenging aspect of the issue is that cyber dangers are increasing, and North America has the largest market share in the global industrial cyber security sector. Numerous businesses in North America are having trouble creating industrial cyber security risk management programmes as a result of rising company fundamentals and the requirement to adopt Industrial Internet of Things (IIoT) technology. Additionally, important companies' increased investment to expand globally is projected to fuel market expansion in North America. The region's expansion is mostly the fault of important firms like CyberArk Software Ltd., Rockwell Automation, Inc., Cisco System, Inc., and others.
Region with highest CAGR:
Asia Pacific is expected to have the highest CAGR rate during the forecast period. A few of the emerging economies in APAC include China and India. Small and medium-sized businesses (SMEs) are prevalent in these nations and employ more than 70% of the workforce. SMEs are unable to adopt robust security procedures in their organisations due to the high expense of executing an industrial control system security project. However, it is anticipated that reasons including expanding company complexity, quick digitization and virtualization, and the expanding Wearables trend would spur SMEs to employ a range of industrial control systems and services. These SMEs may be advantageous to vendors in the industrial cyber security sector who offer products and services to consumers in the manufacturing, transportation, and energy sectors.
Key players in the market
Some of the key players in Industrial Cyber Security market include Fortinet, Inc., Juniper Networks, Inc., IBM Corporation, F5, Inc., Mandiant, Inc., Oracle Corporation, Intel Corporation, CyberArk Software Ltd., Cisco System, Inc., Palo Alto Network, Inc., Check Point Software, Technologies Ltd., Splunk, Inc., Broadcom, Inc., Microsoft Corporation, Imperva, Inc., RSA Security LLC, Siemens AG, Rockwell Automation, Inc., Dell Inc. and Symantec Corporation
Key Developments:
In August 2022, IBM Corporation launched the Secure Access Service Edge (SASE) solution designed to help organizations adopt cloud-delivered security at the edge, closer to users and devices accessing corporate resources. With SASE, software-defined networking and network security technologies are bundled into a single, cloud-based service.
In March 2022, ABB Ltd. (Switzerland) partnered with Nozomi Networks (US), a leading provider of OT and IoT security and visibility solutions, to fulfill the growing demand for improved OT cybersecurity solutions from the energy, process, and hybrid industries. This acquisition enabled ABB to integrate Nozomi Networks’ advanced solutions for operational resiliency and real-time network visibility to assist ABB’s global automation and digitalization customers.
In January 2022, Honeywell International Inc. and Acalvio Technologies (US) teamed up to launch HTDP, a platform designed to detect known and unknown cyberattacks across the OT environments in commercial buildings. The sophisticated, active defense system features autonomous deception tactics to outsmart attackers and provides high-fidelity threat detection.
Types Covered:
• Network Security
• Application Security
• Wireless Security
• Cloud Security
• Endpoint Security
• Other Types
Components Covered:
• Services
• Solutions
• Other Components
Deployment Modes Covered:
• Cloud-based Deployment
• On-premise Deployment
End-Users Covered:
• Transportation & Logistics
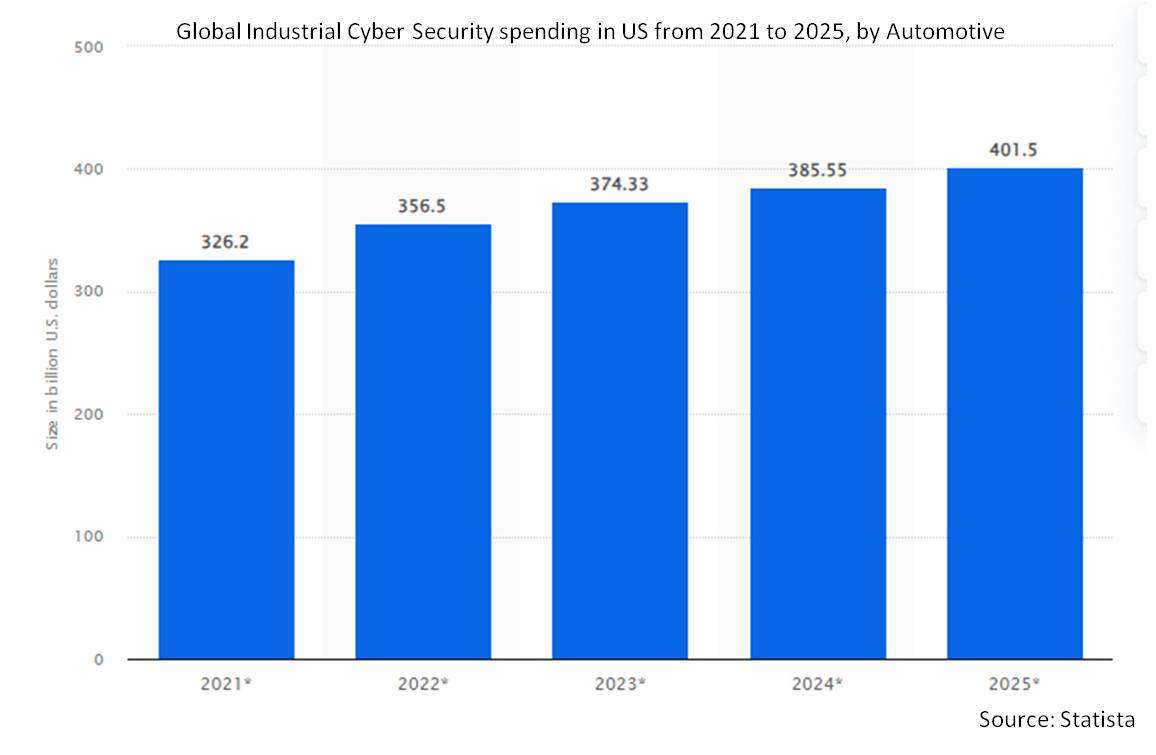
• Automotive
• Electronics & Electrical
• Heavy Manufacturing
• Aerospace & Defence
• Oil and Gas
• Food and Beverages
• Chemicals
• Energy and Power
• Water
• Other End Users
Regions Covered:
• North America
o US
o Canada
o Mexico
• Europe
o Germany
o UK
o Italy
o France
o Spain
o Rest of Europe
• Asia Pacific
o Japan
o China
o India
o Australia
o New Zealand
o South Korea
o Rest of Asia Pacific
• South America
o Argentina
o Brazil
o Chile
o Rest of South America
• Middle East & Africa
o Saudi Arabia
o UAE
o Qatar
o South Africa
o Rest of Middle East & Africa
What our report offers:
- Market share assessments for the regional and country-level segments
- Strategic recommendations for the new entrants
- Covers Market data for the years 2021, 2022, 2023, 2026, and 2030
- Market Trends (Drivers, Constraints, Opportunities, Threats, Challenges, Investment Opportunities, and recommendations)
- Strategic recommendations in key business segments based on the market estimations
- Competitive landscaping mapping the key common trends
- Company profiling with detailed strategies, financials, and recent developments
- Supply chain trends mapping the latest technological advancements
Free Customization Offerings:
All the customers of this report will be entitled to receive one of the following free customization options:
• Company Profiling
o Comprehensive profiling of additional market players (up to 3)
o SWOT Analysis of key players (up to 3)
• Regional Segmentation
o Market estimations, Forecasts and CAGR of any prominent country as per the client's interest (Note: Depends on feasibility check)
• Competitive Benchmarking
Benchmarking of key players based on product portfolio, geographical presence, and strategic alliances
Table of Contents
1 Executive Summary
2 Preface
2.1 Abstract
2.2 Stake Holders
2.3 Research Scope
2.4 Research Methodology
2.4.1 Data Mining
2.4.2 Data Analysis
2.4.3 Data Validation
2.4.4 Research Approach
2.5 Research Sources
2.5.1 Primary Research Sources
2.5.2 Secondary Research Sources
2.5.3 Assumptions
3 Market Trend Analysis
3.1 Introduction
3.2 Drivers
3.3 Restraints
3.4 Opportunities
3.5 Threats
3.6 End User Analysis
3.7 Emerging Markets
3.8 Impact of Covid-19
4 Porters Five Force Analysis
4.1 Bargaining power of suppliers
4.2 Bargaining power of buyers
4.3 Threat of substitutes
4.4 Threat of new entrants
4.5 Competitive rivalry
5 Global Industrial Cyber Security Market, By Security Type
5.1 Introduction
5.2 Network Security
5.3 Application Security
5.4 Wireless Security
5.5 Cloud Security
5.6 Endpoint Security
5.7 Other Types
6 Global Industrial Cyber Security Market, By Component
6.1 Introduction
6.2 Services
6.2.1 Managed Services
6.2.2 Professional Services
6.3 Solutions
6.3.1 Encryption
6.3.2 Unified Threat Management
6.3.3 Antivirus/Antimalware
6.3.4 Security & Vulnerability Management
6.3.5 Web Filtering
6.3.6 Risk & Compliance Management
6.3.7 Data Loss Prevention
6.3.8 Firewalls
6.3.9 Intrusion Detection/Prevention Systems
6.3.10 Disaster Recovery
6.3.11 Identity & Access Management
6.3.12 DDS Management
6.4 Other Components
7 Global Industrial Cyber Security Market, By Deployment Mode
7.1 Introduction
7.2 Cloud-based Deployment
7.3 On-premise Deployment
8 Global Industrial Cyber Security Market, By End User
8.1 Introduction
8.2 Transportation & Logistics
8.3 Automotive
8.4 Electronics & Electrical
8.5 Heavy Manufacturing
8.6 Aerospace & Defense
8.7 Oil and Gas
8.8 Food and Beverages
8.9 Chemicals
8.10 Energy and Power
8.11 Water
8.12 Other End Users
9 Global Industrial Cyber Security Market, By Geography
9.1 Introduction
9.2 North America
9.2.1 US
9.2.2 Canada
9.2.3 Mexico
9.3 Europe
9.3.1 Germany
9.3.2 UK
9.3.3 Italy
9.3.4 France
9.3.5 Spain
9.3.6 Rest of Europe
9.4 Asia Pacific
9.4.1 Japan
9.4.2 China
9.4.3 India
9.4.4 Australia
9.4.5 New Zealand
9.4.6 South Korea
9.4.7 Rest of Asia Pacific
9.5 South America
9.5.1 Argentina
9.5.2 Brazil
9.5.3 Chile
9.5.4 Rest of South America
9.6 Middle East & Africa
9.6.1 Saudi Arabia
9.6.2 UAE
9.6.3 Qatar
9.6.4 South Africa
9.6.5 Rest of Middle East & Africa
10 Key Developments
10.1 Agreements, Partnerships, Collaborations and Joint Ventures
10.2 Acquisitions & Mergers
10.3 New Product Launch
10.4 Expansions
10.5 Other Key Strategies
11 Company Profiling
11.1 Fortinet, Inc.
11.2 Juniper Networks, Inc.
11.3 IBM Corporation
11.4 F5, Inc.
11.5 Mandiant, Inc.
11.6 Oracle Corporation
11.7 Intel Corporation
11.8 CyberArk Software Ltd.
11.9 Cisco System, Inc.
11.10 Palo Alto Network, Inc.
11.11 Check Point Software Technologies Ltd.
11.12 Splunk, Inc.
11.13 Broadcom, Inc.
11.14 Microsoft Corporation
11.15 Imperva, Inc.
11.16 RSA Security LLC
11.17 Siemens AG
11.18 Rockwell Automation, Inc.
11.19 Dell Inc.
11.20 Symantec Corporation
List of Tables
1 Global Industrial Cyber Security Market Outlook, By Region (2021-2030) ($MN)
2 Global Industrial Cyber Security Market Outlook, By Security Type (2021-2030) ($MN)
3 Global Industrial Cyber Security Market Outlook, By Network Security (2021-2030) ($MN)
4 Global Industrial Cyber Security Market Outlook, By Application Security (2021-2030) ($MN)
5 Global Industrial Cyber Security Market Outlook, By Wireless Security (2021-2030) ($MN)
6 Global Industrial Cyber Security Market Outlook, By Cloud Security (2021-2030) ($MN)
7 Global Industrial Cyber Security Market Outlook, By Endpoint Security (2021-2030) ($MN)
8 Global Industrial Cyber Security Market Outlook, By Other Types (2021-2030) ($MN)
9 Global Industrial Cyber Security Market Outlook, By Component (2021-2030) ($MN)
10 Global Industrial Cyber Security Market Outlook, By Services (2021-2030) ($MN)
11 Global Industrial Cyber Security Market Outlook, By Managed Services (2021-2030) ($MN)
12 Global Industrial Cyber Security Market Outlook, By Professional Services (2021-2030) ($MN)
13 Global Industrial Cyber Security Market Outlook, By Solutions (2021-2030) ($MN)
14 Global Industrial Cyber Security Market Outlook, By Encryption (2021-2030) ($MN)
15 Global Industrial Cyber Security Market Outlook, By Unified Threat Management (2021-2030) ($MN)
16 Global Industrial Cyber Security Market Outlook, By Antivirus/Antimalware (2021-2030) ($MN)
17 Global Industrial Cyber Security Market Outlook, By Security & Vulnerability Management (2021-2030) ($MN)
18 Global Industrial Cyber Security Market Outlook, By Web Filtering (2021-2030) ($MN)
19 Global Industrial Cyber Security Market Outlook, By Risk & Compliance Management (2021-2030) ($MN)
20 Global Industrial Cyber Security Market Outlook, By Data Loss Prevention (2021-2030) ($MN)
21 Global Industrial Cyber Security Market Outlook, By Firewalls (2021-2030) ($MN)
22 Global Industrial Cyber Security Market Outlook, By Intrusion Detection/Prevention Systems (2021-2030) ($MN)
23 Global Industrial Cyber Security Market Outlook, By Disaster Recovery (2021-2030) ($MN)
24 Global Industrial Cyber Security Market Outlook, By Identity & Access Management (2021-2030) ($MN)
25 Global Industrial Cyber Security Market Outlook, By DDS Management (2021-2030) ($MN)
26 Global Industrial Cyber Security Market Outlook, By Other Components (2021-2030) ($MN)
27 Global Industrial Cyber Security Market Outlook, By Deployment Mode (2021-2030) ($MN)
28 Global Industrial Cyber Security Market Outlook, By Cloud-based Deployment (2021-2030) ($MN)
29 Global Industrial Cyber Security Market Outlook, By On-premise Deployment (2021-2030) ($MN)
30 Global Industrial Cyber Security Market Outlook, By End User (2021-2030) ($MN)
31 Global Industrial Cyber Security Market Outlook, By Transportation & Logistics (2021-2030) ($MN)
32 Global Industrial Cyber Security Market Outlook, By Automotive (2021-2030) ($MN)
33 Global Industrial Cyber Security Market Outlook, By Electronics & Electrical (2021-2030) ($MN)
34 Global Industrial Cyber Security Market Outlook, By Heavy Manufacturing (2021-2030) ($MN)
35 Global Industrial Cyber Security Market Outlook, By Aerospace & Defense (2021-2030) ($MN)
36 Global Industrial Cyber Security Market Outlook, By Oil and Gas (2021-2030) ($MN)
37 Global Industrial Cyber Security Market Outlook, By Food and Beverages (2021-2030) ($MN)
38 Global Industrial Cyber Security Market Outlook, By Chemicals (2021-2030) ($MN)
39 Global Industrial Cyber Security Market Outlook, By Energy and Power (2021-2030) ($MN)
40 Global Industrial Cyber Security Market Outlook, By Water (2021-2030) ($MN)
41 Global Industrial Cyber Security Market Outlook, By Other End Users (2021-2030) ($MN)
Note: Tables for North America, Europe, APAC, South America, and Middle East & Africa Regions are also represented in the same manner as above.
List of Figures
Figure 1 Global Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 2 North America Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 3 US Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 4 Canada Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 5 Mexico Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 6 Europe Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 7 Germany Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 8 UK Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 9 Italy Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 10 France Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 11 Spain Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 12 Rest of Europe Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 13 Asia Pacific Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 14 Japan Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 15 China Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 16 India Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 17 Australia Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 18 New Zealand Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 19 South Korea Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 20 Rest of Asia Pacific Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 21 South America Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 22 Argentina Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 23 Brazil Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 24 Chile Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 25 Rest of South America Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 26 Middle East & Africa Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 27 Saudi Arabia Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 28 UAE Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 29 Qatar Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 30 South Africa Industrial Cyber Security Market Outlook (2021-2030) ($MN)
Figure 31 Rest of Middle East & Africa Industrial Cyber Security Market Outlook (2021-2030) ($MN)
RESEARCH METHODOLOGY
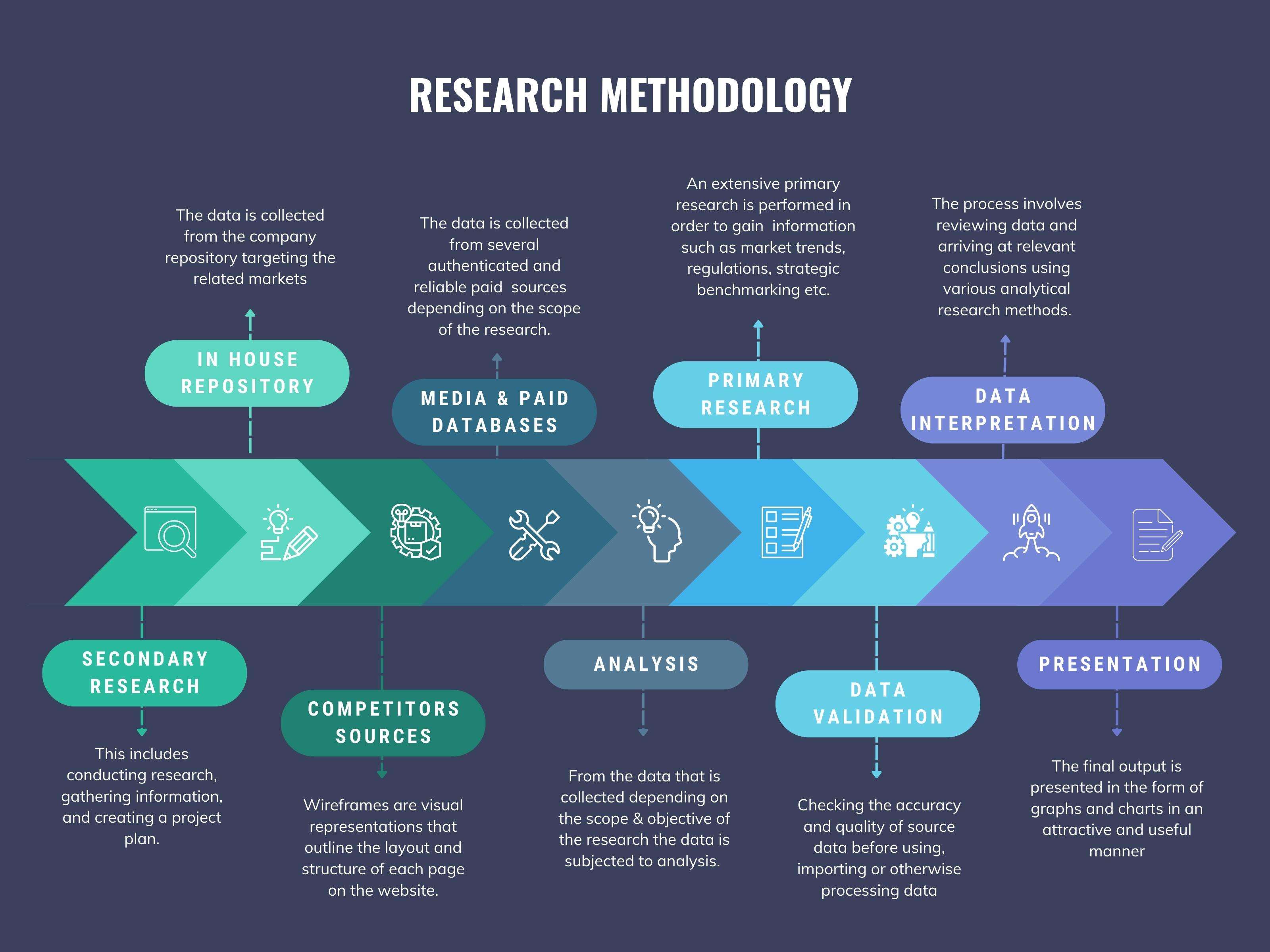
We at ‘Stratistics’ opt for an extensive research approach which involves data mining, data validation, and data analysis. The various research sources include in-house repository, secondary research, competitor’s sources, social media research, client internal data, and primary research.
Our team of analysts prefers the most reliable and authenticated data sources in order to perform the comprehensive literature search. With access to most of the authenticated data bases our team highly considers the best mix of information through various sources to obtain extensive and accurate analysis.
Each report takes an average time of a month and a team of 4 industry analysts. The time may vary depending on the scope and data availability of the desired market report. The various parameters used in the market assessment are standardized in order to enhance the data accuracy.
Data Mining
The data is collected from several authenticated, reliable, paid and unpaid sources and is filtered depending on the scope & objective of the research. Our reports repository acts as an added advantage in this procedure. Data gathering from the raw material suppliers, distributors and the manufacturers is performed on a regular basis, this helps in the comprehensive understanding of the products value chain. Apart from the above mentioned sources the data is also collected from the industry consultants to ensure the objective of the study is in the right direction.
Market trends such as technological advancements, regulatory affairs, market dynamics (Drivers, Restraints, Opportunities and Challenges) are obtained from scientific journals, market related national & international associations and organizations.
Data Analysis
From the data that is collected depending on the scope & objective of the research the data is subjected for the analysis. The critical steps that we follow for the data analysis include:
- Product Lifecycle Analysis
- Competitor analysis
- Risk analysis
- Porters Analysis
- PESTEL Analysis
- SWOT Analysis
The data engineering is performed by the core industry experts considering both the Marketing Mix Modeling and the Demand Forecasting. The marketing mix modeling makes use of multiple-regression techniques to predict the optimal mix of marketing variables. Regression factor is based on a number of variables and how they relate to an outcome such as sales or profits.
Data Validation
The data validation is performed by the exhaustive primary research from the expert interviews. This includes telephonic interviews, focus groups, face to face interviews, and questionnaires to validate our research from all aspects. The industry experts we approach come from the leading firms, involved in the supply chain ranging from the suppliers, distributors to the manufacturers and consumers so as to ensure an unbiased analysis.
We are in touch with more than 15,000 industry experts with the right mix of consultants, CEO's, presidents, vice presidents, managers, experts from both supply side and demand side, executives and so on.
The data validation involves the primary research from the industry experts belonging to:
- Leading Companies
- Suppliers & Distributors
- Manufacturers
- Consumers
- Industry/Strategic Consultants
Apart from the data validation the primary research also helps in performing the fill gap research, i.e. providing solutions for the unmet needs of the research which helps in enhancing the reports quality.
For more details about research methodology, kindly write to us at info@strategymrc.com
Frequently Asked Questions
In case of any queries regarding this report, you can contact the customer service by filing the “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
Yes, the samples are available for all the published reports. You can request them by filling the “Request Sample” option available in this page.
Yes, you can request a sample with your specific requirements. All the customized samples will be provided as per the requirement with the real data masked.
All our reports are available in Digital PDF format. In case if you require them in any other formats, such as PPT, Excel etc you can submit a request through “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
We offer a free 15% customization with every purchase. This requirement can be fulfilled for both pre and post sale. You may send your customization requirements through email at info@strategymrc.com or call us on +1-301-202-5929.
We have 3 different licensing options available in electronic format.
- Single User Licence: Allows one person, typically the buyer, to have access to the ordered product. The ordered product cannot be distributed to anyone else.
- 2-5 User Licence: Allows the ordered product to be shared among a maximum of 5 people within your organisation.
- Corporate License: Allows the product to be shared among all employees of your organisation regardless of their geographical location.
All our reports are typically be emailed to you as an attachment.
To order any available report you need to register on our website. The payment can be made either through CCAvenue or PayPal payments gateways which accept all international cards.
We extend our support to 6 months post sale. A post sale customization is also provided to cover your unmet needs in the report.
Request Customization
We offer complimentary customization of up to 15% with every purchase. To share your customization requirements, feel free to email us at info@strategymrc.com or call us on +1-301-202-5929. .
Please Note: Customization within the 15% threshold is entirely free of charge. If your request exceeds this limit, we will conduct a feasibility assessment. Following that, a detailed quote and timeline will be provided.
WHY CHOOSE US ?

Assured Quality
Best in class reports with high standard of research integrity

24X7 Research Support
Continuous support to ensure the best customer experience.

Free Customization
Adding more values to your product of interest.

Safe & Secure Access
Providing a secured environment for all online transactions.

Trusted by 600+ Brands
Serving the most reputed brands across the world.
