
M2m Security Market
M2M Security Market Forecasts to 2032 - Global Analysis By Type (Hardware Systems and Software Services), Security Type (Device Security, Network Security, Application Security and Cloud Security), Application and By Geography

According to Stratistics MRC, the Global M2M Security Market is accounted for $34.36 billion in 2025 and is expected to reach $59.66 billion by 2032 growing at a CAGR of 8.2% during the forecast period. Machine-to-Machine (M2M) security is essential for ensuring secure and dependable communication between linked devices in sectors like industrial automation, smart grids, healthcare, and the automotive industry. Since M2M communication makes it possible for data to be exchanged automatically without human involvement, it is susceptible to cyber threats such as denial-of-service (DoS) attacks, illegal access, and data breaches. Moreover, access control, intrusion detection systems, encryption, and authentication are all necessary for effective M2M security in order to safeguard private information and guarantee device integrity.
According to a report by the International Data Corporation (IDC), the number of IoT devices has increased from 10 billion in 2019 to 18.5 billion in 2024. As these devices handle professional, financial, and critical business data, the risk of interception is higher, necessitating the adoption of M2M security solutions.
Market Dynamics:
Driver:
Growing data breach and cyber threats
One major factor driving demand for M2M security solutions is the rise in cyber attacks that target M2M networks, including ransom ware, malware, data breaches, and denial-of-service (DoS) attacks. M2M communication offers a potential weakness for cybercriminals to take advantage of since it allows automated data exchange between devices without human intervention. Additionally, cyber threats target industries that store and transmit sensitive data, such as healthcare, automotive, and industrial automation. To protect their networks from possible intrusions, businesses are spending money on strong security frameworks that include firewalls, intrusion detection systems, and end-to-end encryption.
Restraint:
Expensive implementation and upkeep
The implementation of strong M2M security solutions entails high expenses for software, hardware, and qualified cybersecurity staff. Investments in advanced threat detection systems, encryption methods, and secure communication protocols are all necessary for businesses and raise operating costs. Furthermore, technical and financial resources must also be continuously available to maintain and update security frameworks in order to combat changing cyber threats. The adoption of M2M security is often limited by small and medium-sized businesses' (SMEs') inability to set aside adequate funds for it. An additional financial burden is created by the need to upgrade or replace outdated M2M systems in order to ensure compliance with contemporary security standards.
Opportunity:
Growing use of edge computing and 5G
Faster, low-latency communication between devices is being made possible by the rollout of 5G networks and the growing usage of edge computing, which is changing the M2M security environment. 5G is perfect for safe M2M communications in sectors like healthcare, automotive, and industrial automation because it offers more bandwidth and enhanced network dependability. By processing data closer to the source and lowering exposure to cyber threats during data transmission, edge computing further improves security. Moreover, the need for sophisticated M2M security features like AI-driven threat detection, secure network slicing, and end-to-end encryption will increase as businesses embrace 5G and edge solutions more and more, opening up large market opportunities.
Threat:
Absence of uniform security procedures
The lack of internationally recognized security standards is one of the main obstacles to M2M security. The cybersecurity frameworks used by various industries and geographical areas result in disparities in the way M2M security is applied. Vulnerabilities arise from this lack of standardization since certain networks and devices might not adhere to the strictest security requirements. Organizations find it challenging to guarantee end-to-end security throughout their M2M ecosystems due to inconsistent security policies, which also make compliance efforts more difficult. Additionally, cybercriminals can take advantage of weak points in the security chain in the absence of universal security protocols, raising the possibility of data breaches and illegal access.
Covid-19 Impact:
The COVID-19 pandemic significantly impacted the M2M security market by accelerating digital transformation and increasing reliance on connected devices across industries such as healthcare, manufacturing, logistics, and smart cities. M2M communication networks grew quickly as a result of the rise in remote work and automation, which introduced new security flaws. Cybercriminals took advantage of the situation and launched increasingly complex attacks against vital infrastructure, such as ransom ware, phishing, and data breaches. Due to a lack of funding and cybersecurity resources, organizations had trouble protecting cloud-based M2M ecosystems, IoT devices, and remote endpoints.
The Hardware Systems segment is expected to be the largest during the forecast period
The Hardware Systems segment is expected to account for the largest market share during the forecast period. The growing demand for security hardware is driving the software services segment, which is predicted to account for more than 52.7% of the market by 2037. This growth is due to the growing use of IoT devices in a variety of industries and the resulting need for strong software solutions to handle related cybersecurity risks. Moreover, advanced cloud-based M2M security software provides real-time monitoring and updates for large device networks, which in turn encourages the development of solutions that incorporate technologies like artificial intelligence and machine learning.
The Cloud Security segment is expected to have the highest CAGR during the forecast period
Over the forecast period, the Cloud Security segment is predicted to witness the highest growth rate. The growing use of cloud-based infrastructures in a variety of sectors, such as IT & telecom, BFSI, and healthcare, is what is causing this growth. To safeguard apps, data, and systems, strong security solutions are required. Comprehensive cloud security measures are becoming more and more necessary as businesses move their operations to the cloud. Additionally, these measures must address issues like data breaches, unauthorized access, and regulatory compliance. Because of this, the Cloud Security segment is anticipated to grow quickly, which is in line with its vital function in protecting cloud environments in the M2M ecosystem.
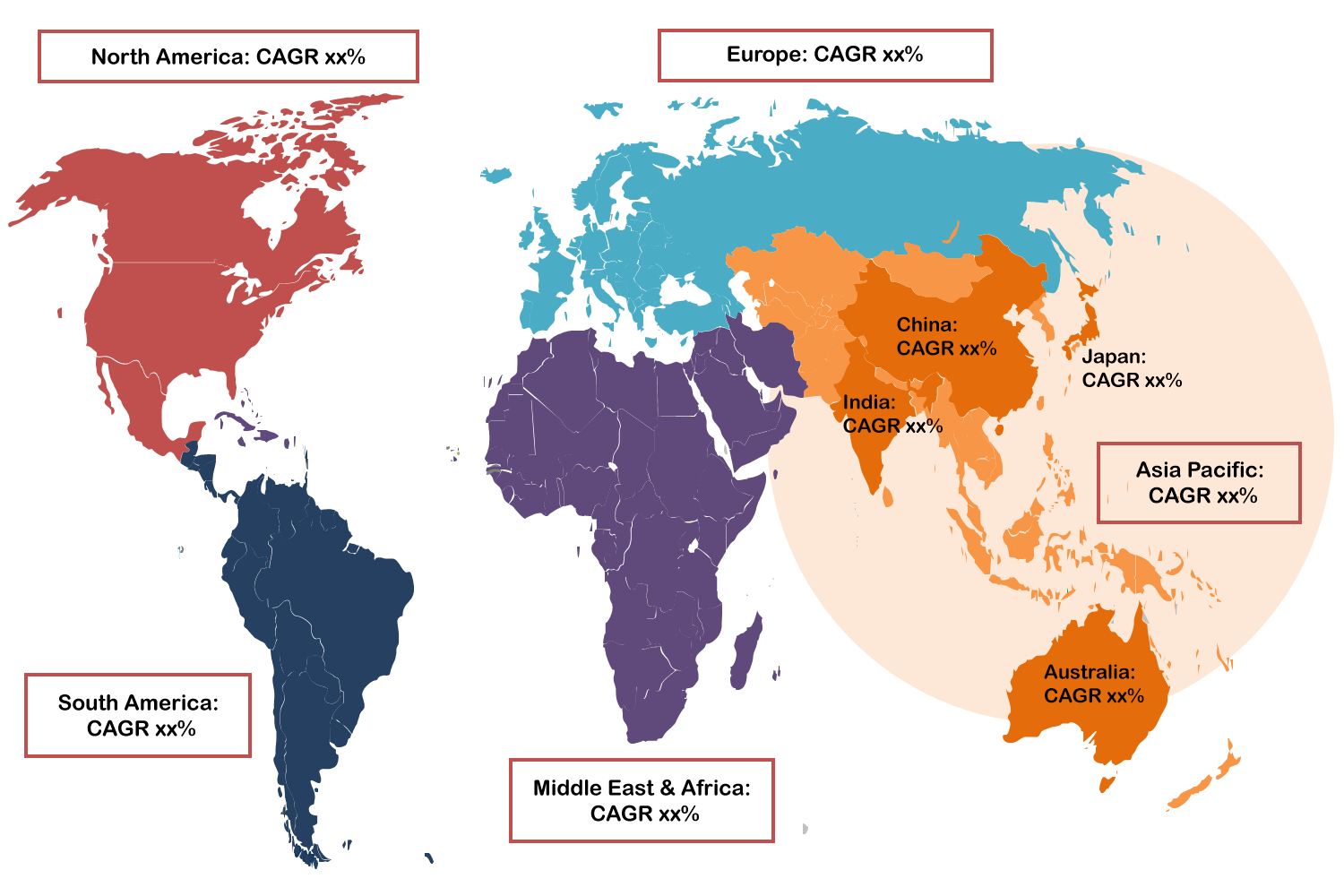
Region with largest share:
During the forecast period, the North America region is expected to hold the largest market share, propelled by the extensive use of IoT and M2M communication technologies in sectors like manufacturing, smart cities, healthcare, and automobiles. The region's concentration of significant cybersecurity solution providers and tech behemoths like Palo Alto Networks, Cisco, and IBM has further bolstered market expansion. Organizations have also been forced to make significant investments in strong M2M security solutions due to strict regulatory frameworks like the Cybersecurity Improvement Act and GDPR compliance in data security.
Region with highest CAGR:
Over the forecast period, the Asia Pacific region is anticipated to exhibit the highest CAGR. The main cause of this quick expansion is the growing use of Internet of Things (IoT) technologies in a variety of sectors, which calls for strong M2M security solutions to guard against online attacks. This trend is being driven by nations like Japan, which have made large investments in IoT infrastructure and placed a greater emphasis on cybersecurity. Moreover, the need for secure communication methods in the region has been further highlighted by the expanding threat landscape, which includes terrorism and cyber attacks.
Key players in the market
Some of the key players in M2M Security market include Cisco Systems, Eurotech Inc, Systech Inc, NetComm Wireless Ltd, PTC Inc, Gemalto, SIMCom Wireless Solutions, Novatel Wireless Inc, Digi International, Kore Wireless Ltd, Numerex Inc and Sierra Wireless Inc.
Key Developments:
In November 2024, Cisco and MGM Resorts International have announced a multi-year whole portfolio agreement (WPA) that will provide MGM Resorts with access to the majority of Cisco's software portfolio. This includes cybersecurity, software-defined networking, software-defined WAN [wide area network], digital experience assurance, full-stack observability, data centre and services.
In September 2024, PTC announced entry into a Strategic Collaboration Agreement (SCA) with Amazon Web Services (AWS) to accelerate the growth of its Onshape® cloud-native computer-aided design (CAD) and product data management (PDM) solution. This collaboration will focus on advancing Onshape product enhancements, customer adoption programs, and artificial intelligence (AI) initiatives, all of which are aimed at helping product designers and engineers create new, high-quality products faster and more efficiently.
In April 2023, KORE Group Holdings, Inc has acquired Twilio's IoT business unit. This acquisition is part of KORE's strategy to become the world's first ""IoT Hyperscaler"" and to provide customers with a unified, seamless approach to launching IoT solutions.
Types Covered:
• Hardware Systems
• Software Services
Security Types Covered:
• Device Security
• Network Security
• Application Security
• Cloud Security
Applications Covered:
• Household
• Industrial
• Retail and Payment Industries
• Logistics and Transportation Industries
• Healthcare
Regions Covered:
• North America
o US
o Canada
o Mexico
• Europe
o Germany
o UK
o Italy
o France
o Spain
o Rest of Europe
• Asia Pacific
o Japan
o China
o India
o Australia
o New Zealand
o South Korea
o Rest of Asia Pacific
• South America
o Argentina
o Brazil
o Chile
o Rest of South America
• Middle East & Africa
o Saudi Arabia
o UAE
o Qatar
o South Africa
o Rest of Middle East & Africa
What our report offers:
- Market share assessments for the regional and country-level segments
- Strategic recommendations for the new entrants
- Covers Market data for the years 2024, 2025, 2026, 2028, and 2032
- Market Trends (Drivers, Constraints, Opportunities, Threats, Challenges, Investment Opportunities, and recommendations)
- Strategic recommendations in key business segments based on the market estimations
- Competitive landscaping mapping the key common trends
- Company profiling with detailed strategies, financials, and recent developments
- Supply chain trends mapping the latest technological advancements
Free Customization Offerings:
All the customers of this report will be entitled to receive one of the following free customization options:
• Company Profiling
o Comprehensive profiling of additional market players (up to 3)
o SWOT Analysis of key players (up to 3)
• Regional Segmentation
o Market estimations, Forecasts and CAGR of any prominent country as per the client's interest (Note: Depends on feasibility check)
• Competitive Benchmarking
o Benchmarking of key players based on product portfolio, geographical presence, and strategic alliances
Table of Contents
1 Executive Summary
2 Preface
2.1 Abstract
2.2 Stake Holders
2.3 Research Scope
2.4 Research Methodology
2.4.1 Data Mining
2.4.2 Data Analysis
2.4.3 Data Validation
2.4.4 Research Approach
2.5 Research Sources
2.5.1 Primary Research Sources
2.5.2 Secondary Research Sources
2.5.3 Assumptions
3 Market Trend Analysis
3.1 Introduction
3.2 Drivers
3.3 Restraints
3.4 Opportunities
3.5 Threats
3.6 Application Analysis
3.7 Emerging Markets
3.8 Impact of Covid-19
4 Porters Five Force Analysis
4.1 Bargaining power of suppliers
4.2 Bargaining power of buyers
4.3 Threat of substitutes
4.4 Threat of new entrants
4.5 Competitive rivalry
5 Global M2M Security Market, By Type
5.1 Introduction
5.2 Hardware Systems
5.3 Software Services
6 Global M2M Security Market, By Security Type
6.1 Introduction
6.2 Device Security
6.3 Network Security
6.4 Application Security
6.5 Cloud Security
7 Global M2M Security Market, By Application
7.1 Introduction
7.2 Household
7.3 Industrial
7.4 Retail and Payment Industries
7.5 Logistics and Transportation Industries
7.6 Healthcare
8 Global M2M Security Market, By Geography
8.1 Introduction
8.2 North America
8.2.1 US
8.2.2 Canada
8.2.3 Mexico
8.3 Europe
8.3.1 Germany
8.3.2 UK
8.3.3 Italy
8.3.4 France
8.3.5 Spain
8.3.6 Rest of Europe
8.4 Asia Pacific
8.4.1 Japan
8.4.2 China
8.4.3 India
8.4.4 Australia
8.4.5 New Zealand
8.4.6 South Korea
8.4.7 Rest of Asia Pacific
8.5 South America
8.5.1 Argentina
8.5.2 Brazil
8.5.3 Chile
8.5.4 Rest of South America
8.6 Middle East & Africa
8.6.1 Saudi Arabia
8.6.2 UAE
8.6.3 Qatar
8.6.4 South Africa
8.6.5 Rest of Middle East & Africa
9 Key Developments
9.1 Agreements, Partnerships, Collaborations and Joint Ventures
9.2 Acquisitions & Mergers
9.3 New Product Launch
9.4 Expansions
9.5 Other Key Strategies
10 Company Profiling
10.1 Cisco Systems
10.2 Eurotech Inc
10.3 Systech Inc
10.4 NetComm Wireless Ltd
10.5 PTC Inc
10.6 Gemalto
10.7 SIMCom Wireless Solutions
10.8 Novatel Wireless Inc
10.9 Digi International
10.10 Kore Wireless Ltd
10.11 Numerex Inc
10.12 Sierra Wireless Inc
List of Tables
1 Global M2M Security Market Outlook, By Region (2024-2032) ($MN)
2 Global M2M Security Market Outlook, By Type (2024-2032) ($MN)
3 Global M2M Security Market Outlook, By Hardware Systems (2024-2032) ($MN)
4 Global M2M Security Market Outlook, By Software Services (2024-2032) ($MN)
5 Global M2M Security Market Outlook, By Security Type (2024-2032) ($MN)
6 Global M2M Security Market Outlook, By Device Security (2024-2032) ($MN)
7 Global M2M Security Market Outlook, By Network Security (2024-2032) ($MN)
8 Global M2M Security Market Outlook, By Application Security (2024-2032) ($MN)
9 Global M2M Security Market Outlook, By Cloud Security (2024-2032) ($MN)
10 Global M2M Security Market Outlook, By Application (2024-2032) ($MN)
11 Global M2M Security Market Outlook, By Household (2024-2032) ($MN)
12 Global M2M Security Market Outlook, By Industrial (2024-2032) ($MN)
13 Global M2M Security Market Outlook, By Retail and Payment Industries (2024-2032) ($MN)
14 Global M2M Security Market Outlook, By Logistics and Transportation Industries (2024-2032) ($MN)
15 Global M2M Security Market Outlook, By Healthcare (2024-2032) ($MN)
16 North America M2M Security Market Outlook, By Country (2024-2032) ($MN)
17 North America M2M Security Market Outlook, By Type (2024-2032) ($MN)
18 North America M2M Security Market Outlook, By Hardware Systems (2024-2032) ($MN)
19 North America M2M Security Market Outlook, By Software Services (2024-2032) ($MN)
20 North America M2M Security Market Outlook, By Security Type (2024-2032) ($MN)
21 North America M2M Security Market Outlook, By Device Security (2024-2032) ($MN)
22 North America M2M Security Market Outlook, By Network Security (2024-2032) ($MN)
23 North America M2M Security Market Outlook, By Application Security (2024-2032) ($MN)
24 North America M2M Security Market Outlook, By Cloud Security (2024-2032) ($MN)
25 North America M2M Security Market Outlook, By Application (2024-2032) ($MN)
26 North America M2M Security Market Outlook, By Household (2024-2032) ($MN)
27 North America M2M Security Market Outlook, By Industrial (2024-2032) ($MN)
28 North America M2M Security Market Outlook, By Retail and Payment Industries (2024-2032) ($MN)
29 North America M2M Security Market Outlook, By Logistics and Transportation Industries (2024-2032) ($MN)
30 North America M2M Security Market Outlook, By Healthcare (2024-2032) ($MN)
31 Europe M2M Security Market Outlook, By Country (2024-2032) ($MN)
32 Europe M2M Security Market Outlook, By Type (2024-2032) ($MN)
33 Europe M2M Security Market Outlook, By Hardware Systems (2024-2032) ($MN)
34 Europe M2M Security Market Outlook, By Software Services (2024-2032) ($MN)
35 Europe M2M Security Market Outlook, By Security Type (2024-2032) ($MN)
36 Europe M2M Security Market Outlook, By Device Security (2024-2032) ($MN)
37 Europe M2M Security Market Outlook, By Network Security (2024-2032) ($MN)
38 Europe M2M Security Market Outlook, By Application Security (2024-2032) ($MN)
39 Europe M2M Security Market Outlook, By Cloud Security (2024-2032) ($MN)
40 Europe M2M Security Market Outlook, By Application (2024-2032) ($MN)
41 Europe M2M Security Market Outlook, By Household (2024-2032) ($MN)
42 Europe M2M Security Market Outlook, By Industrial (2024-2032) ($MN)
43 Europe M2M Security Market Outlook, By Retail and Payment Industries (2024-2032) ($MN)
44 Europe M2M Security Market Outlook, By Logistics and Transportation Industries (2024-2032) ($MN)
45 Europe M2M Security Market Outlook, By Healthcare (2024-2032) ($MN)
46 Asia Pacific M2M Security Market Outlook, By Country (2024-2032) ($MN)
47 Asia Pacific M2M Security Market Outlook, By Type (2024-2032) ($MN)
48 Asia Pacific M2M Security Market Outlook, By Hardware Systems (2024-2032) ($MN)
49 Asia Pacific M2M Security Market Outlook, By Software Services (2024-2032) ($MN)
50 Asia Pacific M2M Security Market Outlook, By Security Type (2024-2032) ($MN)
51 Asia Pacific M2M Security Market Outlook, By Device Security (2024-2032) ($MN)
52 Asia Pacific M2M Security Market Outlook, By Network Security (2024-2032) ($MN)
53 Asia Pacific M2M Security Market Outlook, By Application Security (2024-2032) ($MN)
54 Asia Pacific M2M Security Market Outlook, By Cloud Security (2024-2032) ($MN)
55 Asia Pacific M2M Security Market Outlook, By Application (2024-2032) ($MN)
56 Asia Pacific M2M Security Market Outlook, By Household (2024-2032) ($MN)
57 Asia Pacific M2M Security Market Outlook, By Industrial (2024-2032) ($MN)
58 Asia Pacific M2M Security Market Outlook, By Retail and Payment Industries (2024-2032) ($MN)
59 Asia Pacific M2M Security Market Outlook, By Logistics and Transportation Industries (2024-2032) ($MN)
60 Asia Pacific M2M Security Market Outlook, By Healthcare (2024-2032) ($MN)
61 South America M2M Security Market Outlook, By Country (2024-2032) ($MN)
62 South America M2M Security Market Outlook, By Type (2024-2032) ($MN)
63 South America M2M Security Market Outlook, By Hardware Systems (2024-2032) ($MN)
64 South America M2M Security Market Outlook, By Software Services (2024-2032) ($MN)
65 South America M2M Security Market Outlook, By Security Type (2024-2032) ($MN)
66 South America M2M Security Market Outlook, By Device Security (2024-2032) ($MN)
67 South America M2M Security Market Outlook, By Network Security (2024-2032) ($MN)
68 South America M2M Security Market Outlook, By Application Security (2024-2032) ($MN)
69 South America M2M Security Market Outlook, By Cloud Security (2024-2032) ($MN)
70 South America M2M Security Market Outlook, By Application (2024-2032) ($MN)
71 South America M2M Security Market Outlook, By Household (2024-2032) ($MN)
72 South America M2M Security Market Outlook, By Industrial (2024-2032) ($MN)
73 South America M2M Security Market Outlook, By Retail and Payment Industries (2024-2032) ($MN)
74 South America M2M Security Market Outlook, By Logistics and Transportation Industries (2024-2032) ($MN)
75 South America M2M Security Market Outlook, By Healthcare (2024-2032) ($MN)
76 Middle East & Africa M2M Security Market Outlook, By Country (2024-2032) ($MN)
77 Middle East & Africa M2M Security Market Outlook, By Type (2024-2032) ($MN)
78 Middle East & Africa M2M Security Market Outlook, By Hardware Systems (2024-2032) ($MN)
79 Middle East & Africa M2M Security Market Outlook, By Software Services (2024-2032) ($MN)
80 Middle East & Africa M2M Security Market Outlook, By Security Type (2024-2032) ($MN)
81 Middle East & Africa M2M Security Market Outlook, By Device Security (2024-2032) ($MN)
82 Middle East & Africa M2M Security Market Outlook, By Network Security (2024-2032) ($MN)
83 Middle East & Africa M2M Security Market Outlook, By Application Security (2024-2032) ($MN)
84 Middle East & Africa M2M Security Market Outlook, By Cloud Security (2024-2032) ($MN)
85 Middle East & Africa M2M Security Market Outlook, By Application (2024-2032) ($MN)
86 Middle East & Africa M2M Security Market Outlook, By Household (2024-2032) ($MN)
87 Middle East & Africa M2M Security Market Outlook, By Industrial (2024-2032) ($MN)
88 Middle East & Africa M2M Security Market Outlook, By Retail and Payment Industries (2024-2032) ($MN)
89 Middle East & Africa M2M Security Market Outlook, By Logistics and Transportation Industries (2024-2032) ($MN)
90 Middle East & Africa M2M Security Market Outlook, By Healthcare (2024-2032) ($MN)
List of Figures
RESEARCH METHODOLOGY
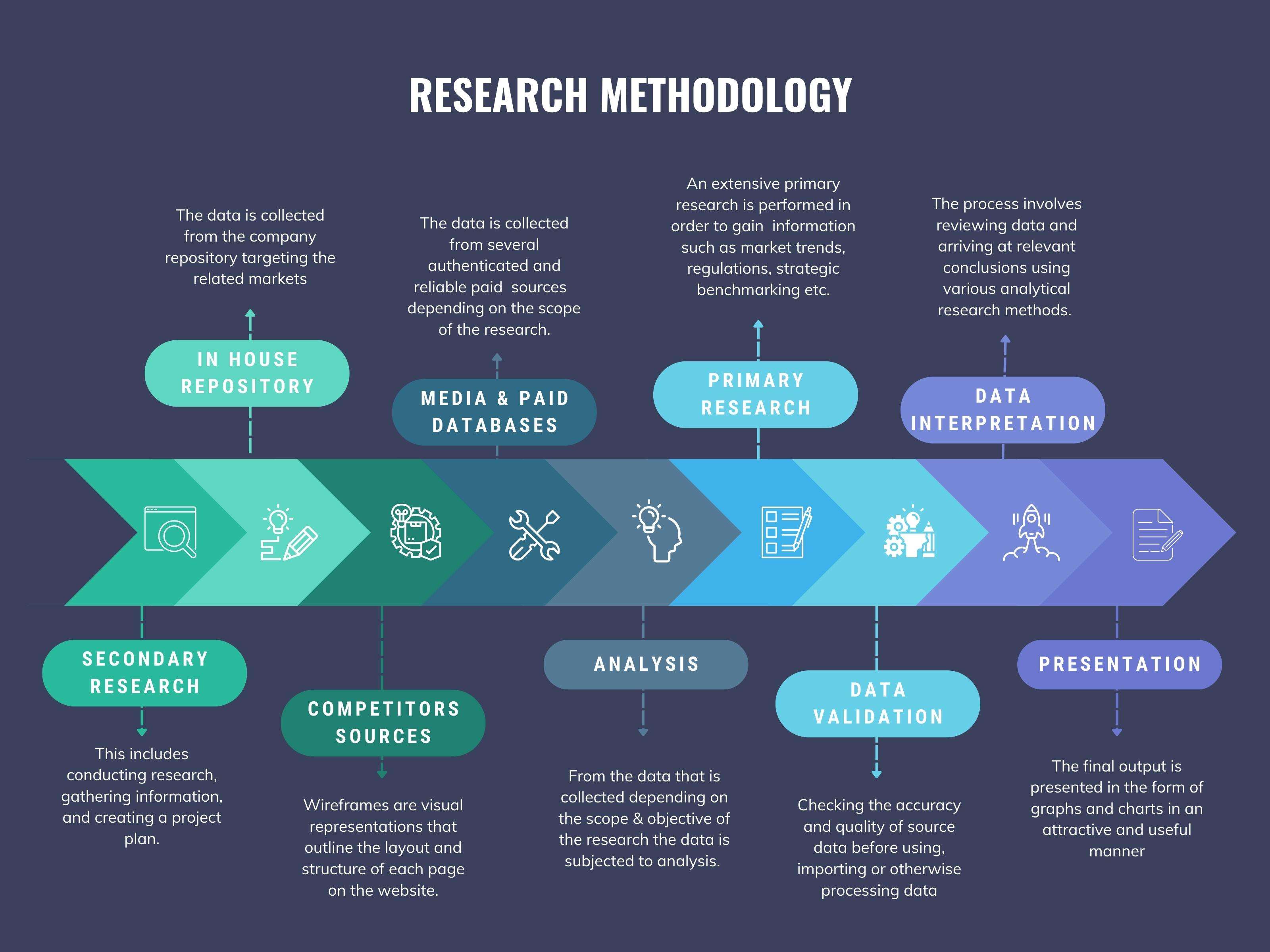
We at ‘Stratistics’ opt for an extensive research approach which involves data mining, data validation, and data analysis. The various research sources include in-house repository, secondary research, competitor’s sources, social media research, client internal data, and primary research.
Our team of analysts prefers the most reliable and authenticated data sources in order to perform the comprehensive literature search. With access to most of the authenticated data bases our team highly considers the best mix of information through various sources to obtain extensive and accurate analysis.
Each report takes an average time of a month and a team of 4 industry analysts. The time may vary depending on the scope and data availability of the desired market report. The various parameters used in the market assessment are standardized in order to enhance the data accuracy.
Data Mining
The data is collected from several authenticated, reliable, paid and unpaid sources and is filtered depending on the scope & objective of the research. Our reports repository acts as an added advantage in this procedure. Data gathering from the raw material suppliers, distributors and the manufacturers is performed on a regular basis, this helps in the comprehensive understanding of the products value chain. Apart from the above mentioned sources the data is also collected from the industry consultants to ensure the objective of the study is in the right direction.
Market trends such as technological advancements, regulatory affairs, market dynamics (Drivers, Restraints, Opportunities and Challenges) are obtained from scientific journals, market related national & international associations and organizations.
Data Analysis
From the data that is collected depending on the scope & objective of the research the data is subjected for the analysis. The critical steps that we follow for the data analysis include:
- Product Lifecycle Analysis
- Competitor analysis
- Risk analysis
- Porters Analysis
- PESTEL Analysis
- SWOT Analysis
The data engineering is performed by the core industry experts considering both the Marketing Mix Modeling and the Demand Forecasting. The marketing mix modeling makes use of multiple-regression techniques to predict the optimal mix of marketing variables. Regression factor is based on a number of variables and how they relate to an outcome such as sales or profits.
Data Validation
The data validation is performed by the exhaustive primary research from the expert interviews. This includes telephonic interviews, focus groups, face to face interviews, and questionnaires to validate our research from all aspects. The industry experts we approach come from the leading firms, involved in the supply chain ranging from the suppliers, distributors to the manufacturers and consumers so as to ensure an unbiased analysis.
We are in touch with more than 15,000 industry experts with the right mix of consultants, CEO's, presidents, vice presidents, managers, experts from both supply side and demand side, executives and so on.
The data validation involves the primary research from the industry experts belonging to:
- Leading Companies
- Suppliers & Distributors
- Manufacturers
- Consumers
- Industry/Strategic Consultants
Apart from the data validation the primary research also helps in performing the fill gap research, i.e. providing solutions for the unmet needs of the research which helps in enhancing the reports quality.
For more details about research methodology, kindly write to us at info@strategymrc.com
Frequently Asked Questions
In case of any queries regarding this report, you can contact the customer service by filing the “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
Yes, the samples are available for all the published reports. You can request them by filling the “Request Sample” option available in this page.
Yes, you can request a sample with your specific requirements. All the customized samples will be provided as per the requirement with the real data masked.
All our reports are available in Digital PDF format. In case if you require them in any other formats, such as PPT, Excel etc you can submit a request through “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
We offer a free 15% customization with every purchase. This requirement can be fulfilled for both pre and post sale. You may send your customization requirements through email at info@strategymrc.com or call us on +1-301-202-5929.
We have 3 different licensing options available in electronic format.
- Single User Licence: Allows one person, typically the buyer, to have access to the ordered product. The ordered product cannot be distributed to anyone else.
- 2-5 User Licence: Allows the ordered product to be shared among a maximum of 5 people within your organisation.
- Corporate License: Allows the product to be shared among all employees of your organisation regardless of their geographical location.
All our reports are typically be emailed to you as an attachment.
To order any available report you need to register on our website. The payment can be made either through CCAvenue or PayPal payments gateways which accept all international cards.
We extend our support to 6 months post sale. A post sale customization is also provided to cover your unmet needs in the report.
Request Customization
We offer complimentary customization of up to 15% with every purchase. To share your customization requirements, feel free to email us at info@strategymrc.com or call us on +1-301-202-5929. .
Please Note: Customization within the 15% threshold is entirely free of charge. If your request exceeds this limit, we will conduct a feasibility assessment. Following that, a detailed quote and timeline will be provided.
WHY CHOOSE US ?

Assured Quality
Best in class reports with high standard of research integrity

24X7 Research Support
Continuous support to ensure the best customer experience.

Free Customization
Adding more values to your product of interest.

Safe & Secure Access
Providing a secured environment for all online transactions.

Trusted by 600+ Brands
Serving the most reputed brands across the world.
