
Database Encryption Market
Database Encryption - Global Market Outlook (2019-2027)

According to Stratistics MRC, the Global Database Encryption market is accounted for $745.43 million in 2019 and is expected to reach $5,013.02 million by 2027 growing at a CAGR of 26.9% during the forecast period. Growing demand for cloud-based database, availability of flexible encryption software and need of organizations to comply with regulatory standards are the major factors driving the market growth. However, high cost encryption solutions are restraining the market growth.
Database encryption refers to using encryption techniques to convert plain text data on database into ciphertext to secure the integrity of enterprise database. Database security, a major concern for enterprises, primarily consists of access control and database encryption. Access control systems have been widely implemented for database security which is not the case with database encryption.
Based on the application, the government and public sectors segment is going to have lucrative growth during the forecast period due to the rising utilization of database encryption solution by government entities and enterprises. By geography, North America is going to have high growth during the forecast period as most of the small and medium sized enterprises in this region are integrating technology which is leading to the requirement of efficient database encryption software.
Some of the key players profiled in the Database Encryption Market include Check Point Software Technologies Ltd., EMC Corporation, Gemalto, IBM Corporation, Intel, Microsoft Corporation, Oracle, Symantec Corporation, Trend Micro Inc and Win Magic Inc.
Types Covered:
• Application- Level Encryption
• Client-Side Encryption
• Column-Level Encryption
• Database Management System (DBMS)-Level Encryption
• File-System Encryption
• Indexing Encrypted Data
• Key Management
• Transparent Encryption
Deployments Covered:
• On Premises
• Cloud
Encryption Methods Covered:
• Hashing
• Symmetric Method
• Asymmetric Method
Operational Models Covered:
• Data-at-Rest
• Data-in-Motion
Applications Covered:
• Aerospace & Defense
• Banking, Financial Services, and Insurance (BFSI)
• Government & Public Sectors
• Healthcare
• Information Technology (IT) & Telecom
• Retail and E-commerce
Attack Types Covered:
• Database Operational Model
• Attack Comprising Security
End Users Covered:
• Small and Medium Sized Businesses
• Enterprises
• Manufacturing
Regions Covered:
• North America
o US
o Canada
o Mexico
• Europe
o Germany
o UK
o Italy
o France
o Spain
o Rest of Europe
• Asia Pacific
o Japan
o China
o India
o Australia
o New Zealand
o South Korea
o Rest of Asia Pacific
• South America
o Argentina
o Brazil
o Chile
o Rest of South America
• Middle East & Africa
o Saudi Arabia
o UAE
o Qatar
o South Africa
o Rest of Middle East & Africa
What our report offers:
- Market share assessments for the regional and country-level segments
- Strategic recommendations for the new entrants
- Covers Market data for the years 2018, 2019, 2020, 2024 and 2027
- Market Trends (Drivers, Constraints, Opportunities, Threats, Challenges, Investment Opportunities, and recommendations)
- Strategic recommendations in key business segments based on the market estimations
- Competitive landscaping mapping the key common trends
- Company profiling with detailed strategies, financials, and recent developments
- Supply chain trends mapping the latest technological advancements
Free Customization Offerings:
All the customers of this report will be entitled to receive one of the following free customization options:
• Company Profiling
o Comprehensive profiling of additional market players (up to 3)
o SWOT Analysis of key players (up to 3)
• Regional Segmentation
o Market estimations, Forecasts and CAGR of any prominent country as per the client's interest (Note: Depends on feasibility check)
• Competitive Benchmarking
o Benchmarking of key players based on product portfolio, geographical presence, and strategic alliances
Table of Contents
1 Executive Summary
2 Preface
2.1 Abstract
2.2 Stake Holders
2.3 Research Scope
2.4 Research Methodology
2.4.1 Data Mining
2.4.2 Data Analysis
2.4.3 Data Validation
2.4.4 Research Approach
2.5 Research Sources
2.5.1 Primary Research Sources
2.5.2 Secondary Research Sources
2.5.3 Assumptions
3 Market Trend Analysis
3.1 Introduction
3.2 Drivers
3.3 Restraints
3.4 Opportunities
3.5 Threats
3.6 Application Analysis
3.7 End User Analysis
3.8 Emerging Markets
3.9 Impact of Covid-19
4 Porters Five Force Analysis
4.1 Bargaining power of suppliers
4.2 Bargaining power of buyers
4.3 Threat of substitutes
4.4 Threat of new entrants
4.5 Competitive rivalry
5 Global Database Encryption Market, By Type
5.1 Introduction
5.2 Application- Level Encryption
5.3 Client-Side Encryption
5.4 Column-Level Encryption
5.5 Database Management System (DBMS)-Level Encryption
5.6 File-System Encryption
5.7 Indexing Encrypted Data
5.8 Key Management
5.9 Transparent Encryption
6 Global Database Encryption Market, By Deployment
6.1 Introduction
6.2 On Premises
6.3 Cloud
6.3.1 Public Cloud
6.3.2 Private Cloud
6.3.3 Hybrid Cloud
7 Global Database Encryption Market, By Encryption Method
7.1 Introduction
7.2 Hashing
7.3 Symmetric Method
7.4 Asymmetric Method
8 Global Database Encryption Market, By Operational Model
8.1 Introduction
8.2 Data-at-Rest
8.3 Data-in-Motion
9 Global Database Encryption Market, By Application
9.1 Introduction
9.2 Aerospace & Defense
9.3 Banking, Financial Services, and Insurance (BFSI)
9.4 Government & Public Sectors
9.5 Healthcare
9.6 Information Technology (IT) & Telecom
9.7 Retail and E-commerce
10 Global Database Encryption Market, By Attack Type
10.1 Introduction
10.2 Database Operational Model
10.2.1 Data-in-Motion
10.2.2 Data-in-Use
10.2.3 Data-at-Rest
10.3 Attack Comprising Security
10.3.1 Intruder
10.3.2 Insider
10.3.3 Administrator
10.3.4 Passive Attack
10.3.4.1 Static Leakage
10.3.4.2 Linkage Leakage
10.3.4.3 Dynamic Leakage
10.3.5 Active Attack
10.3.5.1 Spoofing
10.3.5.2 Splicing
10.3.5.3 Replay
11 Global Database Encryption Market, By End User
11.1 Introduction
11.2 Small and Medium Sized Businesses
11.3 Enterprises
11.4 Manufacturing
12 Global Database Encryption Market, By Geography
12.1 Introduction
12.2 North America
12.2.1 US
12.2.2 Canada
12.2.3 Mexico
12.3 Europe
12.3.1 Germany
12.3.2 UK
12.3.3 Italy
12.3.4 France
12.3.5 Spain
12.3.6 Rest of Europe
12.4 Asia Pacific
12.4.1 Japan
12.4.2 China
12.4.3 India
12.4.4 Australia
12.4.5 New Zealand
12.4.6 South Korea
12.4.7 Rest of Asia Pacific
12.5 South America
12.5.1 Argentina
12.5.2 Brazil
12.5.3 Chile
12.5.4 Rest of South America
12.6 Middle East & Africa
12.6.1 Saudi Arabia
12.6.2 UAE
12.6.3 Qatar
12.6.4 South Africa
12.6.5 Rest of Middle East & Africa
13 Key Developments
13.1 Agreements, Partnerships, Collaborations and Joint Ventures
13.2 Acquisitions & Mergers
13.3 New Product Launch
13.4 Expansions
13.5 Other Key Strategies
14 Company Profiling
14.1 Check Point Software Technologies Ltd.
14.2 EMC Corporation
14.3 Gemalto
14.4 IBM Corporation
14.5 Intel
14.6 Microsoft Corporation
14.7 Oracle
14.8 Symantec Corporation
14.9 Trend Micro Inc
14.10 Win Magic Inc
List of Tables
1 Global Database Encryption Market Outlook, By Region (2018-2027) (US $MN)
2 Global Database Encryption Market Outlook, By Type (2018-2027) (US $MN)
3 Global Database Encryption Market Outlook, By Application- Level Encryption (2018-2027) (US $MN)
4 Global Database Encryption Market Outlook, By Client-Side Encryption (2018-2027) (US $MN)
5 Global Database Encryption Market Outlook, By Column-Level Encryption (2018-2027) (US $MN)
6 Global Database Encryption Market Outlook, By DataBase Management System (DBMS)-Level Encryption (2018-2027) (US $MN)
7 Global Database Encryption Market Outlook, By File-System Encryption (2018-2027) (US $MN)
8 Global Database Encryption Market Outlook, By Indexing Encrypted Data (2018-2027) (US $MN)
9 Global Database Encryption Market Outlook, By Key Management (2018-2027) (US $MN)
10 Global Database Encryption Market Outlook, By Transparent Encryption (2018-2027) (US $MN)
11 Global Database Encryption Market Outlook, By Deployment (2018-2027) (US $MN)
12 Global Database Encryption Market Outlook, By On Premises (2018-2027) (US $MN)
13 Global Database Encryption Market Outlook, By Cloud (2018-2027) (US $MN)
14 Global Database Encryption Market Outlook, By Public Cloud (2018-2027) (US $MN)
15 Global Database Encryption Market Outlook, By Private Cloud (2018-2027) (US $MN)
16 Global Database Encryption Market Outlook, By Hybrid Cloud (2018-2027) (US $MN)
17 Global Database Encryption Market Outlook, By Encryption Method (2018-2027) (US $MN)
18 Global Database Encryption Market Outlook, By Hashing (2018-2027) (US $MN)
19 Global Database Encryption Market Outlook, By Symmetric Method (2018-2027) (US $MN)
20 Global Database Encryption Market Outlook, By Asymmetric Method (2018-2027) (US $MN)
21 Global Database Encryption Market Outlook, By Operational Model (2018-2027) (US $MN)
22 Global Database Encryption Market Outlook, By Data-at-Rest (2018-2027) (US $MN)
23 Global Database Encryption Market Outlook, By Data-in-Motion (2018-2027) (US $MN)
24 Global Database Encryption Market Outlook, By Application (2018-2027) (US $MN)
25 Global Database Encryption Market Outlook, By Aerospace & Defense (2018-2027) (US $MN)
26 Global Database Encryption Market Outlook, By Banking, Financial Services, and Insurance (BFSI) (2018-2027) (US $MN)
27 Global Database Encryption Market Outlook, By Government & Public Sectors (2018-2027) (US $MN)
28 Global Database Encryption Market Outlook, By Healthcare (2018-2027) (US $MN)
29 Global Database Encryption Market Outlook, By Information Technology (IT) & Telecom (2018-2027) (US $MN)
30 Global Database Encryption Market Outlook, By Retail and E-commerce (2018-2027) (US $MN)
31 Global Database Encryption Market Outlook, By Attack Type (2018-2027) (US $MN)
32 Global Database Encryption Market Outlook, By Database operational model (2018-2027) (US $MN)
33 Global Database Encryption Market Outlook, By Data-in-Motion (2018-2027) (US $MN)
34 Global Database Encryption Market Outlook, By Data-in-Use (2018-2027) (US $MN)
35 Global Database Encryption Market Outlook, By Data-at-Rest (2018-2027) (US $MN)
36 Global Database Encryption Market Outlook, By Attack Comprising Security (2018-2027) (US $MN)
37 Global Database Encryption Market Outlook, By Intruder (2018-2027) (US $MN)
38 Global Database Encryption Market Outlook, By Insider (2018-2027) (US $MN)
39 Global Database Encryption Market Outlook, By Administrator (2018-2027) (US $MN)
40 Global Database Encryption Market Outlook, By Passive Attack (2018-2027) (US $MN)
41 Global Database Encryption Market Outlook, By Active Attack (2018-2027) (US $MN)
42 Global Database Encryption Market Outlook, By End User (2018-2027) (US $MN)
43 Global Database Encryption Market Outlook, By Small and Medium Sized Businesses (2018-2027) (US $MN)
44 Global Database Encryption Market Outlook, By Enterprises (2018-2027) (US $MN)
45 Global Database Encryption Market Outlook, By Manufacturing (2018-2027) (US $MN)
Note: Tables for North America, Europe, Asia Pacific, South America and Middle East & Africa are represented in the same manner as above.
List of Figures
RESEARCH METHODOLOGY
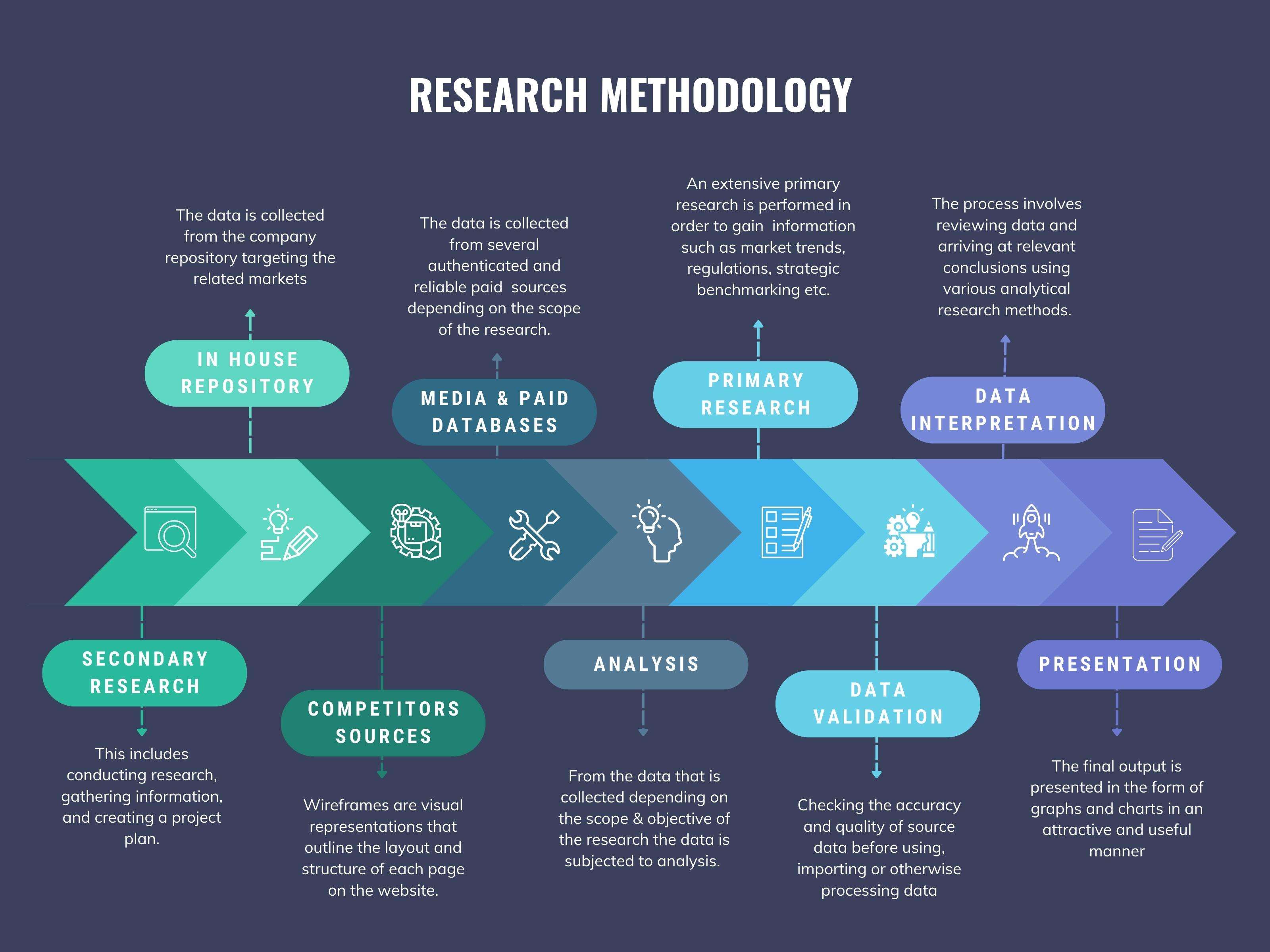
We at ‘Stratistics’ opt for an extensive research approach which involves data mining, data validation, and data analysis. The various research sources include in-house repository, secondary research, competitor’s sources, social media research, client internal data, and primary research.
Our team of analysts prefers the most reliable and authenticated data sources in order to perform the comprehensive literature search. With access to most of the authenticated data bases our team highly considers the best mix of information through various sources to obtain extensive and accurate analysis.
Each report takes an average time of a month and a team of 4 industry analysts. The time may vary depending on the scope and data availability of the desired market report. The various parameters used in the market assessment are standardized in order to enhance the data accuracy.
Data Mining
The data is collected from several authenticated, reliable, paid and unpaid sources and is filtered depending on the scope & objective of the research. Our reports repository acts as an added advantage in this procedure. Data gathering from the raw material suppliers, distributors and the manufacturers is performed on a regular basis, this helps in the comprehensive understanding of the products value chain. Apart from the above mentioned sources the data is also collected from the industry consultants to ensure the objective of the study is in the right direction.
Market trends such as technological advancements, regulatory affairs, market dynamics (Drivers, Restraints, Opportunities and Challenges) are obtained from scientific journals, market related national & international associations and organizations.
Data Analysis
From the data that is collected depending on the scope & objective of the research the data is subjected for the analysis. The critical steps that we follow for the data analysis include:
- Product Lifecycle Analysis
- Competitor analysis
- Risk analysis
- Porters Analysis
- PESTEL Analysis
- SWOT Analysis
The data engineering is performed by the core industry experts considering both the Marketing Mix Modeling and the Demand Forecasting. The marketing mix modeling makes use of multiple-regression techniques to predict the optimal mix of marketing variables. Regression factor is based on a number of variables and how they relate to an outcome such as sales or profits.
Data Validation
The data validation is performed by the exhaustive primary research from the expert interviews. This includes telephonic interviews, focus groups, face to face interviews, and questionnaires to validate our research from all aspects. The industry experts we approach come from the leading firms, involved in the supply chain ranging from the suppliers, distributors to the manufacturers and consumers so as to ensure an unbiased analysis.
We are in touch with more than 15,000 industry experts with the right mix of consultants, CEO's, presidents, vice presidents, managers, experts from both supply side and demand side, executives and so on.
The data validation involves the primary research from the industry experts belonging to:
- Leading Companies
- Suppliers & Distributors
- Manufacturers
- Consumers
- Industry/Strategic Consultants
Apart from the data validation the primary research also helps in performing the fill gap research, i.e. providing solutions for the unmet needs of the research which helps in enhancing the reports quality.
For more details about research methodology, kindly write to us at info@strategymrc.com
Frequently Asked Questions
In case of any queries regarding this report, you can contact the customer service by filing the “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
Yes, the samples are available for all the published reports. You can request them by filling the “Request Sample” option available in this page.
Yes, you can request a sample with your specific requirements. All the customized samples will be provided as per the requirement with the real data masked.
All our reports are available in Digital PDF format. In case if you require them in any other formats, such as PPT, Excel etc you can submit a request through “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
We offer a free 15% customization with every purchase. This requirement can be fulfilled for both pre and post sale. You may send your customization requirements through email at info@strategymrc.com or call us on +1-301-202-5929.
We have 3 different licensing options available in electronic format.
- Single User Licence: Allows one person, typically the buyer, to have access to the ordered product. The ordered product cannot be distributed to anyone else.
- 2-5 User Licence: Allows the ordered product to be shared among a maximum of 5 people within your organisation.
- Corporate License: Allows the product to be shared among all employees of your organisation regardless of their geographical location.
All our reports are typically be emailed to you as an attachment.
To order any available report you need to register on our website. The payment can be made either through CCAvenue or PayPal payments gateways which accept all international cards.
We extend our support to 6 months post sale. A post sale customization is also provided to cover your unmet needs in the report.
Request Customization
We offer complimentary customization of up to 15% with every purchase. To share your customization requirements, feel free to email us at info@strategymrc.com or call us on +1-301-202-5929. .
Please Note: Customization within the 15% threshold is entirely free of charge. If your request exceeds this limit, we will conduct a feasibility assessment. Following that, a detailed quote and timeline will be provided.
WHY CHOOSE US ?

Assured Quality
Best in class reports with high standard of research integrity

24X7 Research Support
Continuous support to ensure the best customer experience.

Free Customization
Adding more values to your product of interest.

Safe & Secure Access
Providing a secured environment for all online transactions.

Trusted by 600+ Brands
Serving the most reputed brands across the world.
