
Cyber Security Managed Services Market
Cyber Security Managed Services Market Forecasts to 2032 - Global Analysis By Service (Managed Detection and Response (MDR), Incident Management, Managed Vulnerability, Identity and Access Solution and Other Services), Security Type, Deployment Mode, Enterprise Type, End User and By Geography

|
Years Covered |
2024-2032 |
|
Estimated Year Value (2025) |
US $20.39 BN |
|
Projected Year Value (2032) |
US $50.42 BN |
|
CAGR (2025 - 2032) |
13.8% |
|
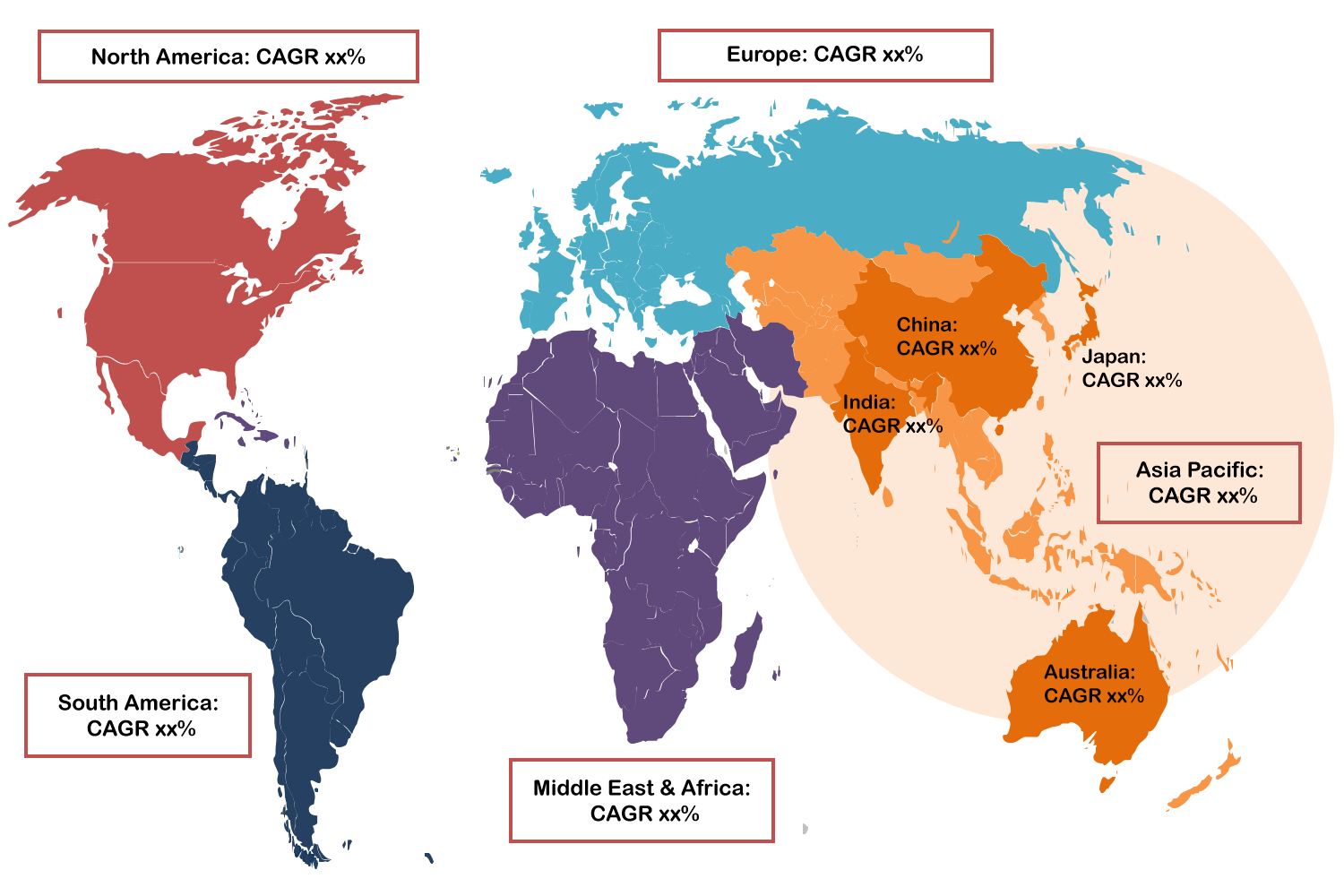
Regions Covered |
North America, Europe, Asia Pacific, South America, and Middle East & Africa |
|
Countries Covered |
US, Canada, Mexico, Germany, UK, Italy, France, Spain, Japan, China, India, Australia, New Zealand, South Korea, Rest of Asia Pacific, South America, Argentina, Brazil, Chile, Middle East & Africa, Saudi Arabia, UAE, Qatar, and South Africa |
|
Largest Market |
North America |
|
Highest Growing Market |
Asia Pacific |
According to Stratistics MRC, the Global Cyber Security Managed Services Market is accounted for $20.39 billion in 2025 and is expected to reach $50.42 billion by 2032 growing at a CAGR of 13.8% during the forecast period. Cyber Security Managed Services are contracted solutions offered by specialized outside vendors to keep an eye on, control, and enhance a company's security setup. These services usually consist of vulnerability assessments, firewall and antivirus management, threat detection and response, compliance assistance, and security incident management. Without the high expenses of maintaining in-house teams, businesses can benefit from managed services' round-the-clock protection from cyber threats, access to knowledgeable security specialists, and cutting-edge tools. Moreover, for companies looking to improve their cyber resilience while concentrating on core functions, this strategy is extremely beneficial.
According to the Data Security Council of India (DSCI), India has over 400 cyber security companies, many of which emphasize managed security services and system integration. This reflects India's growing prominence in the global cyber security landscape.

Market Dynamics:
Driver:
Growing intricacy of cyber threats
Businesses find it difficult to stay up with the latest threats as cyber attacks become more complex, ranging from ransom ware and advanced persistent threats (APTs) to zero-day vulnerabilities. Many organizations lack the in-house advanced threat detection technologies, analytics, and expertise that managed security service providers (MSSPs) bring. Additionally, one of the main reasons businesses are switching to managed services is the capacity to proactively monitor and address such threats around the clock.
Restraint:
Concerns regarding data control and privacy
The reluctance of organizations to allow third-party vendors to handle sensitive data is one of the biggest obstacles. Access to vital IT systems, infrastructure, and private data is frequently necessary for managed service providers to deliver efficient security services. This raises questions regarding possible data leaks, misuse, and illegal access. Financial, healthcare, and defense sectors are particularly wary because of stringent data protection laws. Furthermore, the advantages of outsourcing are outweighed by the perceived risk of data exposure for certain businesses.
Opportunity:
Growth of cloud-based managed security services
Security services that are natively integrated with cloud environments are becoming more and more in demand as cloud adoption accelerates across industries. MSSPs can benefit from this change by providing specialized cloud security solutions, such as identity management, cloud workload protection, and cloud access security brokers (CASBs). Moreover, there will be substantial growth opportunities for MSSPs that provide smooth cloud integration, visibility, and compliance support as enterprises transition to hybrid and multi-cloud technologies.
Threat:
Growing market saturation and competition
There are many service providers fighting for market share in the crowded cyber security managed services sector. Competition is increasing as a result of big players, smaller niche suppliers, and even tech giants providing cloud security services. Price wars may ensue, which would lower MSSPs' profit margins. Furthermore, as the market becomes oversaturated with comparable offerings, the growth of service providers may make it more difficult for companies to choose the most trustworthy and appropriate partners.
Covid-19 Impact:
The COVID-19 pandemic had a major effect on the market for managed services for cyber security because it sped up the adoption of cloud-based solutions and remote work, which increased the attack surface for cybercriminals. Moreover, the need for strong cyber security services increased as companies adopted remote and hybrid work models, which in turn increased demand for managed security solutions. But the pandemic also exposed weaknesses in many organizations' current security architectures, which led to a greater dependence on MSSPs for incident response, threat detection, and ongoing monitoring.
The managed detection and response (MDR) segment is expected to be the largest during the forecast period
The managed detection and response (MDR) segment is expected to account for the largest market share during the forecast period. Continuous monitoring, threat detection, and incident response are all provided by MDR services, giving businesses the cutting-edge tools they need to identify and stop cyber security threats instantly. Businesses need proactive security measures as cyber attacks get more complex, and MDR successfully meets these needs by utilizing automated tools, machine learning, and skilled analysts to react swiftly to incidents. Additionally, the demand for MDR services has increased due to the increasing frequency of cyber threats and the requirement for round-the-clock security monitoring, making it an essential part of businesses' cyber security plans.
The endpoint security segment is expected to have the highest CAGR during the forecast period
Over the forecast period, the endpoint security segment is predicted to witness the highest growth rate. Mobile devices, IoT endpoints, and remote work are all growing in popularity, leaving organizations with more entry points that are susceptible to cyber attacks. By offering automated response, threat detection, and ongoing monitoring for all connected devices, managed endpoint security services mitigate these risks. Advanced, managed protection is in high demand due to the increase in ransom ware, phishing, and zero-day attacks that target endpoints specifically. Furthermore, companies are looking for solutions that guarantee security outside of the conventional network perimeter.
Region with largest share:
During the forecast period, the North America region is expected to hold the largest market share, driven by the prevalence of cyber threats, the existence of large technology companies, and sophisticated digital infrastructure. Because of the early adoption of cloud computing, IoT, and remote work models in the region, the attack surface has grown, necessitating significant investments in managed security solutions from organizations. Moreover, the U.S. and Canadian governments and healthcare and financial sectors place a high priority on cyber security, which propels market expansion.
Region with highest CAGR:
Over the forecast period, the Asia Pacific region is anticipated to exhibit the highest CAGR, driven by rising internet usage, quickening digital transformation, and escalating cyber threats in emerging economies. Cloud adoption, e-commerce, and mobile connectivity are on the rise in nations like China, India, Japan, and South Korea, which has greatly increased the digital attack surface. Additionally, businesses are turning to managed services as a result of growing needs for scalable, affordable cyber security solutions, changing regulatory frameworks, and increased awareness of data protection.
Key players in the market
Some of the key players in Cyber Security Managed Services Market include Atos SE, IBM Corporation, HCL Technologies, Secureworks, Inc., Tata Consultancy Services Limited, Microsoft, Check Point Software Technologies Ltd., Palo Alto Networks, Symantec (Broadcom), Trustwave Holdings, Inc., Wipro, Cisco, SentinelOne Inc and Fortinet Inc.
Key Developments:
In March 2025, Tata Consultancy Services (TCS), India’s largest IT services company, is acquiring 100 per cent equity share of Darshita Southern India Happy Homes for Rs 2,250 crore. The acquisition is focused on acquiring the land and building of Darshita to expand TCS’s delivery centre.
In December 2024, Atos announces that it has signed with Unisys an agreement to resolve the lawsuit filed by Unisys against Atos and two Atos employees in the U.S. District Court for the Eastern District of Pennsylvania. The terms of the settlement are confidential. The settlement will have only a limited impact on Atos’ net debt and leverage with respect to its projections for Q4 2024 and for 2025.
In July 2024, IBM announced that it has secured a five-year contract with $26 million in initial funding from the U.S. Agency for International Development (USAID) to support its Cybersecurity Protection and Response (CPR) program aimed to expand and enhance the agency's cybersecurity response support for host governments in the Europe and Eurasia (E&E) region.
Services Covered:
• Managed Detection and Response (MDR)
• Incident Management
• Managed Vulnerability
• Identity and Access Solution
• Other Services
Security Types Covered:
• Network Security
• Endpoint Security
• Application Security
• Other Security Types
Deployment Modes Covered:
• On-premise
• Cloud
Enterprise Types Covered:
• Small & Medium Size Enterprise
• Large Enterprise
End Users Covered:
• Banking, Financial Services and Insurance (BFSI)
• IT & Telecom
• Retail
• Healthcare
• Government
• Manufacturing
• Travel & Transportation
• Energy and Utilities
• Other End Users
Regions Covered:
• North America
o US
o Canada
o Mexico
• Europe
o Germany
o UK
o Italy
o France
o Spain
o Rest of Europe
• Asia Pacific
o Japan
o China
o India
o Australia
o New Zealand
o South Korea
o Rest of Asia Pacific
• South America
o Argentina
o Brazil
o Chile
o Rest of South America
• Middle East & Africa
o Saudi Arabia
o UAE
o Qatar
o South Africa
o Rest of Middle East & Africa
What our report offers:
- Market share assessments for the regional and country-level segments
- Strategic recommendations for the new entrants
- Covers Market data for the years 2024, 2025, 2026, 2028, and 2032
- Market Trends (Drivers, Constraints, Opportunities, Threats, Challenges, Investment Opportunities, and recommendations)
- Strategic recommendations in key business segments based on the market estimations
- Competitive landscaping mapping the key common trends
- Company profiling with detailed strategies, financials, and recent developments
- Supply chain trends mapping the latest technological advancements
Free Customization Offerings:
All the customers of this report will be entitled to receive one of the following free customization options:
• Company Profiling
o Comprehensive profiling of additional market players (up to 3)
o SWOT Analysis of key players (up to 3)
• Regional Segmentation
o Market estimations, Forecasts and CAGR of any prominent country as per the client's interest (Note: Depends on feasibility check)
• Competitive Benchmarking
o Benchmarking of key players based on product portfolio, geographical presence, and strategic alliances
Table of Contents
1 Executive Summary
2 Preface
2.1 Abstract
2.2 Stake Holders
2.3 Research Scope
2.4 Research Methodology
2.4.1 Data Mining
2.4.2 Data Analysis
2.4.3 Data Validation
2.4.4 Research Approach
2.5 Research Sources
2.5.1 Primary Research Sources
2.5.2 Secondary Research Sources
2.5.3 Assumptions
3 Market Trend Analysis
3.1 Introduction
3.2 Drivers
3.3 Restraints
3.4 Opportunities
3.5 Threats
3.6 End User Analysis
3.7 Emerging Markets
3.8 Impact of Covid-19
4 Porters Five Force Analysis
4.1 Bargaining power of suppliers
4.2 Bargaining power of buyers
4.3 Threat of substitutes
4.4 Threat of new entrants
4.5 Competitive rivalry
5 Global Cyber Security Managed Services Market, By Service
5.1 Introduction
5.2 Managed Detection and Response (MDR)
5.3 Incident Management
5.4 Managed Vulnerability
5.5 Identity and Access Solution
5.6 Other Services
6 Global Cyber Security Managed Services Market, By Security Type
6.1 Introduction
6.2 Network Security
6.3 Endpoint Security
6.4 Application Security
6.5 Other Security Types
7 Global Cyber Security Managed Services Market, By Deployment Mode
7.1 Introduction
7.2 On-premise
7.3 Cloud
8 Global Cyber Security Managed Services Market, By Enterprise Type
8.1 Introduction
8.2 Small & Medium Size Enterprise
8.3 Large Enterprise
9 Global Cyber Security Managed Services Market, By End User
9.1 Introduction
9.2 Banking, Financial Services and Insurance (BFSI)
9.3 IT & Telecom
9.4 Retail
9.5 Healthcare
9.6 Government
9.7 Manufacturing
9.8 Travel & Transportation
9.9 Energy and Utilities
9.10 Other End Users
10 Global Cyber Security Managed Services Market, By Geography
10.1 Introduction
10.2 North America
10.2.1 US
10.2.2 Canada
10.2.3 Mexico
10.3 Europe
10.3.1 Germany
10.3.2 UK
10.3.3 Italy
10.3.4 France
10.3.5 Spain
10.3.6 Rest of Europe
10.4 Asia Pacific
10.4.1 Japan
10.4.2 China
10.4.3 India
10.4.4 Australia
10.4.5 New Zealand
10.4.6 South Korea
10.4.7 Rest of Asia Pacific
10.5 South America
10.5.1 Argentina
10.5.2 Brazil
10.5.3 Chile
10.5.4 Rest of South America
10.6 Middle East & Africa
10.6.1 Saudi Arabia
10.6.2 UAE
10.6.3 Qatar
10.6.4 South Africa
10.6.5 Rest of Middle East & Africa
11 Key Developments
11.1 Agreements, Partnerships, Collaborations and Joint Ventures
11.2 Acquisitions & Mergers
11.3 New Product Launch
11.4 Expansions
11.5 Other Key Strategies
12 Company Profiling
12.1 Atos SE
12.2 IBM Corporation
12.3 HCL Technologies
12.4 Secureworks, Inc.
12.5 Tata Consultancy Services Limited
12.6 Microsoft
12.7 Check Point Software Technologies Ltd.
12.8 Palo Alto Networks
12.9 Symantec (Broadcom)
12.10 Trustwave Holdings, Inc.
12.11 Wipro
12.12 Cisco
12.13 SentinelOne Inc
12.14 Fortinet Inc
List of Tables
1 Global Cyber Security Managed Services Market Outlook, By Region (2024-2032) ($MN)
2 Global Cyber Security Managed Services Market Outlook, By Service (2024-2032) ($MN)
3 Global Cyber Security Managed Services Market Outlook, By Managed Detection and Response (MDR) (2024-2032) ($MN)
4 Global Cyber Security Managed Services Market Outlook, By Incident Management (2024-2032) ($MN)
5 Global Cyber Security Managed Services Market Outlook, By Managed Vulnerability (2024-2032) ($MN)
6 Global Cyber Security Managed Services Market Outlook, By Identity and Access Solution (2024-2032) ($MN)
7 Global Cyber Security Managed Services Market Outlook, By Other Services (2024-2032) ($MN)
8 Global Cyber Security Managed Services Market Outlook, By Security Type (2024-2032) ($MN)
9 Global Cyber Security Managed Services Market Outlook, By Network Security (2024-2032) ($MN)
10 Global Cyber Security Managed Services Market Outlook, By Endpoint Security (2024-2032) ($MN)
11 Global Cyber Security Managed Services Market Outlook, By Application Security (2024-2032) ($MN)
12 Global Cyber Security Managed Services Market Outlook, By Other Security Types (2024-2032) ($MN)
13 Global Cyber Security Managed Services Market Outlook, By Deployment Mode (2024-2032) ($MN)
14 Global Cyber Security Managed Services Market Outlook, By On-premise (2024-2032) ($MN)
15 Global Cyber Security Managed Services Market Outlook, By Cloud (2024-2032) ($MN)
16 Global Cyber Security Managed Services Market Outlook, By Enterprise Type (2024-2032) ($MN)
17 Global Cyber Security Managed Services Market Outlook, By Small & Medium Size Enterprise (2024-2032) ($MN)
18 Global Cyber Security Managed Services Market Outlook, By Large Enterprise (2024-2032) ($MN)
19 Global Cyber Security Managed Services Market Outlook, By End User (2024-2032) ($MN)
20 Global Cyber Security Managed Services Market Outlook, By Banking, Financial Services and Insurance (BFSI) (2024-2032) ($MN)
21 Global Cyber Security Managed Services Market Outlook, By IT & Telecom (2024-2032) ($MN)
22 Global Cyber Security Managed Services Market Outlook, By Retail (2024-2032) ($MN)
23 Global Cyber Security Managed Services Market Outlook, By Healthcare (2024-2032) ($MN)
24 Global Cyber Security Managed Services Market Outlook, By Government (2024-2032) ($MN)
25 Global Cyber Security Managed Services Market Outlook, By Manufacturing (2024-2032) ($MN)
26 Global Cyber Security Managed Services Market Outlook, By Travel & Transportation (2024-2032) ($MN)
27 Global Cyber Security Managed Services Market Outlook, By Energy and Utilities (2024-2032) ($MN)
28 Global Cyber Security Managed Services Market Outlook, By Other End Users (2024-2032) ($MN)
Note: Tables for North America, Europe, APAC, South America, and Middle East & Africa Regions are also represented in the same manner as above.
List of Figures
RESEARCH METHODOLOGY
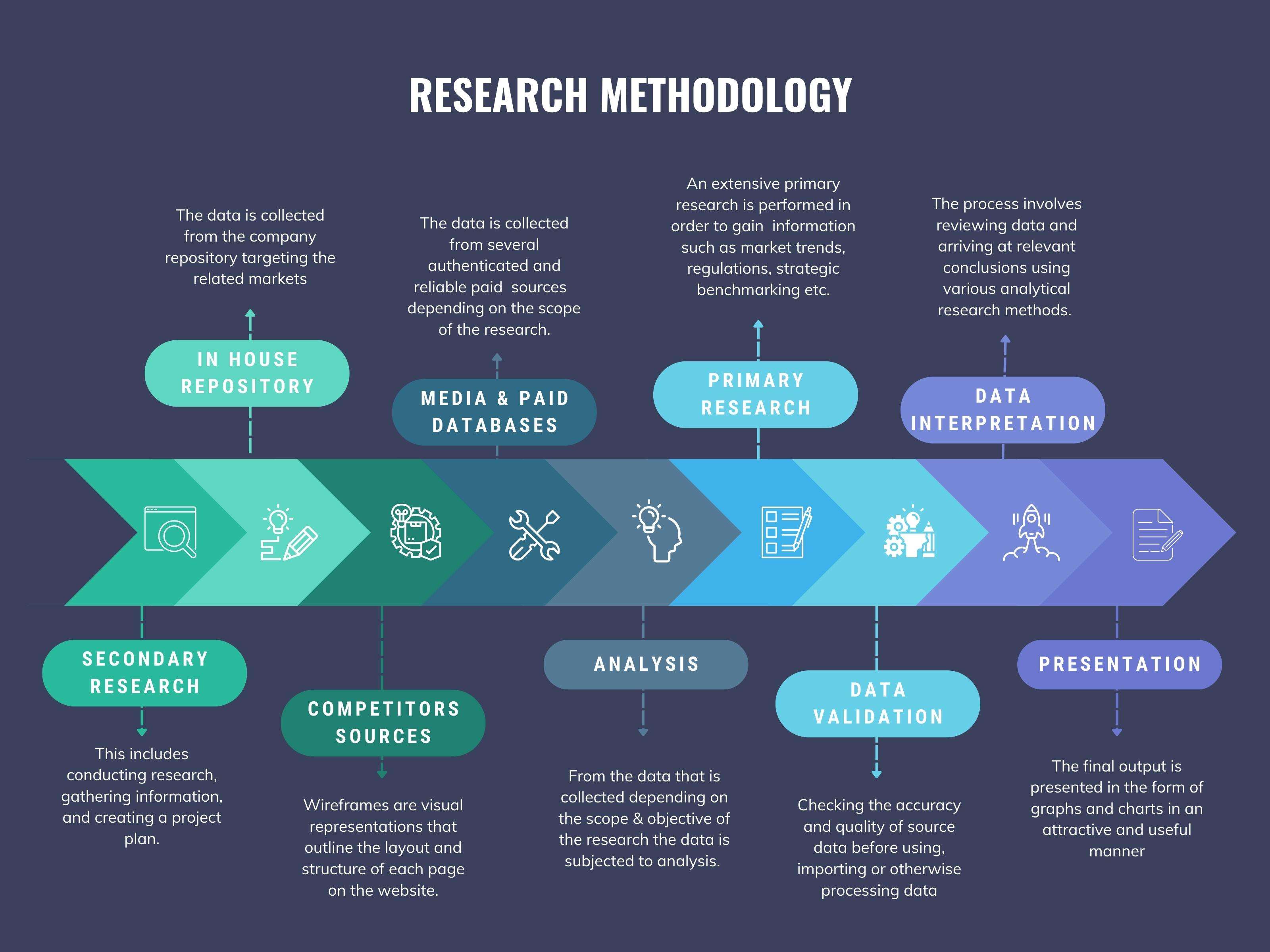
We at ‘Stratistics’ opt for an extensive research approach which involves data mining, data validation, and data analysis. The various research sources include in-house repository, secondary research, competitor’s sources, social media research, client internal data, and primary research.
Our team of analysts prefers the most reliable and authenticated data sources in order to perform the comprehensive literature search. With access to most of the authenticated data bases our team highly considers the best mix of information through various sources to obtain extensive and accurate analysis.
Each report takes an average time of a month and a team of 4 industry analysts. The time may vary depending on the scope and data availability of the desired market report. The various parameters used in the market assessment are standardized in order to enhance the data accuracy.
Data Mining
The data is collected from several authenticated, reliable, paid and unpaid sources and is filtered depending on the scope & objective of the research. Our reports repository acts as an added advantage in this procedure. Data gathering from the raw material suppliers, distributors and the manufacturers is performed on a regular basis, this helps in the comprehensive understanding of the products value chain. Apart from the above mentioned sources the data is also collected from the industry consultants to ensure the objective of the study is in the right direction.
Market trends such as technological advancements, regulatory affairs, market dynamics (Drivers, Restraints, Opportunities and Challenges) are obtained from scientific journals, market related national & international associations and organizations.
Data Analysis
From the data that is collected depending on the scope & objective of the research the data is subjected for the analysis. The critical steps that we follow for the data analysis include:
- Product Lifecycle Analysis
- Competitor analysis
- Risk analysis
- Porters Analysis
- PESTEL Analysis
- SWOT Analysis
The data engineering is performed by the core industry experts considering both the Marketing Mix Modeling and the Demand Forecasting. The marketing mix modeling makes use of multiple-regression techniques to predict the optimal mix of marketing variables. Regression factor is based on a number of variables and how they relate to an outcome such as sales or profits.
Data Validation
The data validation is performed by the exhaustive primary research from the expert interviews. This includes telephonic interviews, focus groups, face to face interviews, and questionnaires to validate our research from all aspects. The industry experts we approach come from the leading firms, involved in the supply chain ranging from the suppliers, distributors to the manufacturers and consumers so as to ensure an unbiased analysis.
We are in touch with more than 15,000 industry experts with the right mix of consultants, CEO's, presidents, vice presidents, managers, experts from both supply side and demand side, executives and so on.
The data validation involves the primary research from the industry experts belonging to:
- Leading Companies
- Suppliers & Distributors
- Manufacturers
- Consumers
- Industry/Strategic Consultants
Apart from the data validation the primary research also helps in performing the fill gap research, i.e. providing solutions for the unmet needs of the research which helps in enhancing the reports quality.
For more details about research methodology, kindly write to us at info@strategymrc.com
Frequently Asked Questions
In case of any queries regarding this report, you can contact the customer service by filing the “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
Yes, the samples are available for all the published reports. You can request them by filling the “Request Sample” option available in this page.
Yes, you can request a sample with your specific requirements. All the customized samples will be provided as per the requirement with the real data masked.
All our reports are available in Digital PDF format. In case if you require them in any other formats, such as PPT, Excel etc you can submit a request through “Inquiry Before Buy” form available on the right hand side. You may also contact us through email: info@strategymrc.com or phone: +1-301-202-5929
We offer a free 15% customization with every purchase. This requirement can be fulfilled for both pre and post sale. You may send your customization requirements through email at info@strategymrc.com or call us on +1-301-202-5929.
We have 3 different licensing options available in electronic format.
- Single User Licence: Allows one person, typically the buyer, to have access to the ordered product. The ordered product cannot be distributed to anyone else.
- 2-5 User Licence: Allows the ordered product to be shared among a maximum of 5 people within your organisation.
- Corporate License: Allows the product to be shared among all employees of your organisation regardless of their geographical location.
All our reports are typically be emailed to you as an attachment.
To order any available report you need to register on our website. The payment can be made either through CCAvenue or PayPal payments gateways which accept all international cards.
We extend our support to 6 months post sale. A post sale customization is also provided to cover your unmet needs in the report.
Request Customization
We offer complimentary customization of up to 15% with every purchase. To share your customization requirements, feel free to email us at info@strategymrc.com or call us on +1-301-202-5929. .
Please Note: Customization within the 15% threshold is entirely free of charge. If your request exceeds this limit, we will conduct a feasibility assessment. Following that, a detailed quote and timeline will be provided.
WHY CHOOSE US ?

Assured Quality
Best in class reports with high standard of research integrity

24X7 Research Support
Continuous support to ensure the best customer experience.

Free Customization
Adding more values to your product of interest.

Safe & Secure Access
Providing a secured environment for all online transactions.

Trusted by 600+ Brands
Serving the most reputed brands across the world.
